.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
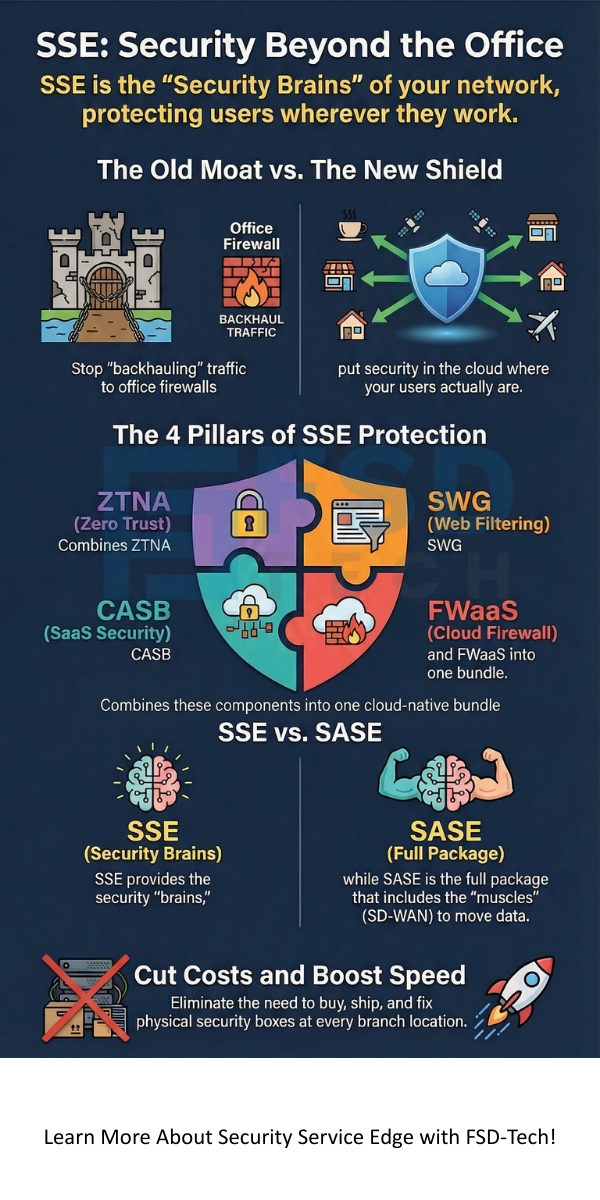
Security Service Edge refers to a modern way of keeping your digital world safe by moving security tools from your office to the cloud. To be honest, we've all been there—struggling with a dozen different security boxes that just don't talk to each other. This old way of doing things is getting too slow and expensive for today’s fast world.
Picture this: your team is working from home, your data is in the cloud, and your office is just one of many "edges". How do you keep it all safe without losing your mind? That’s where Security Service Edge (SSE) comes in to save the day. It’s part of a bigger idea called SASE that simplifies your whole network.
But what does it actually do for you? Let's dive into why this shift matters and how it can help your business grow.
In simple terms, SSE is a bundle of security services delivered through the web. Instead of buying separate firewalls and web filters for every office, you get them all in one place. Gartner coined this term to describe the security side of the Secure Access Service Edge (SASE) framework.
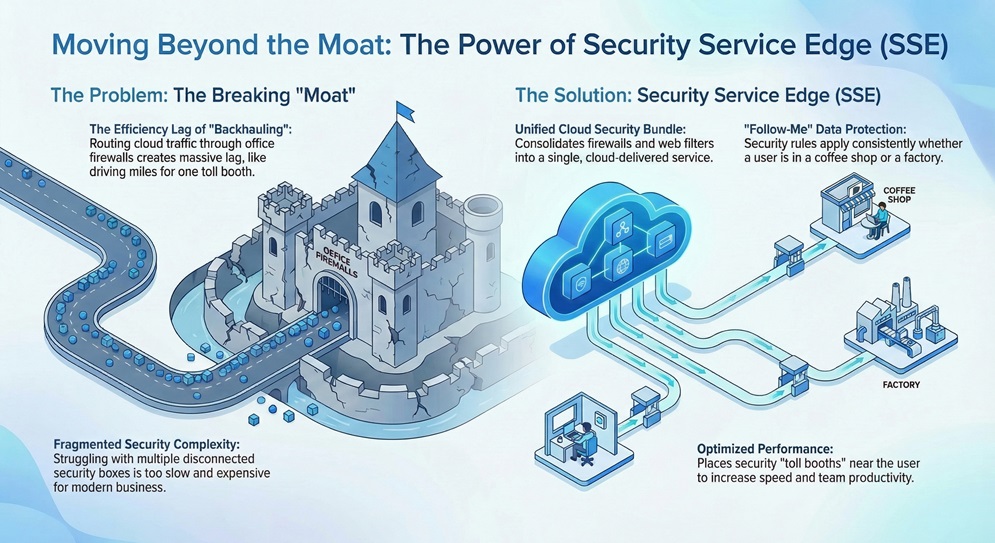
Think of it like a security guard that follows your data everywhere it goes. Whether you're in a coffee shop or a factory, the same rules apply. This makes your life easier because you only have one system to manage.
Historically, we built "moats" around our data centers. We put big firewalls at the front door and thought we were safe. But now, the data has left the building.
Here is the thing: when your apps move to the cloud, "backhauling" traffic to the office creates a massive lag. It’s like driving twenty miles out of your way just to go through a specific toll booth. It just doesn't make sense anymore.
Security Service Edge fixes this by putting the security "toll booth" right where you are. This speeds up your internet and keeps your team productive.
Also Read: Cloud-Native Architecture: Why SASE is the Future of Global Networking?
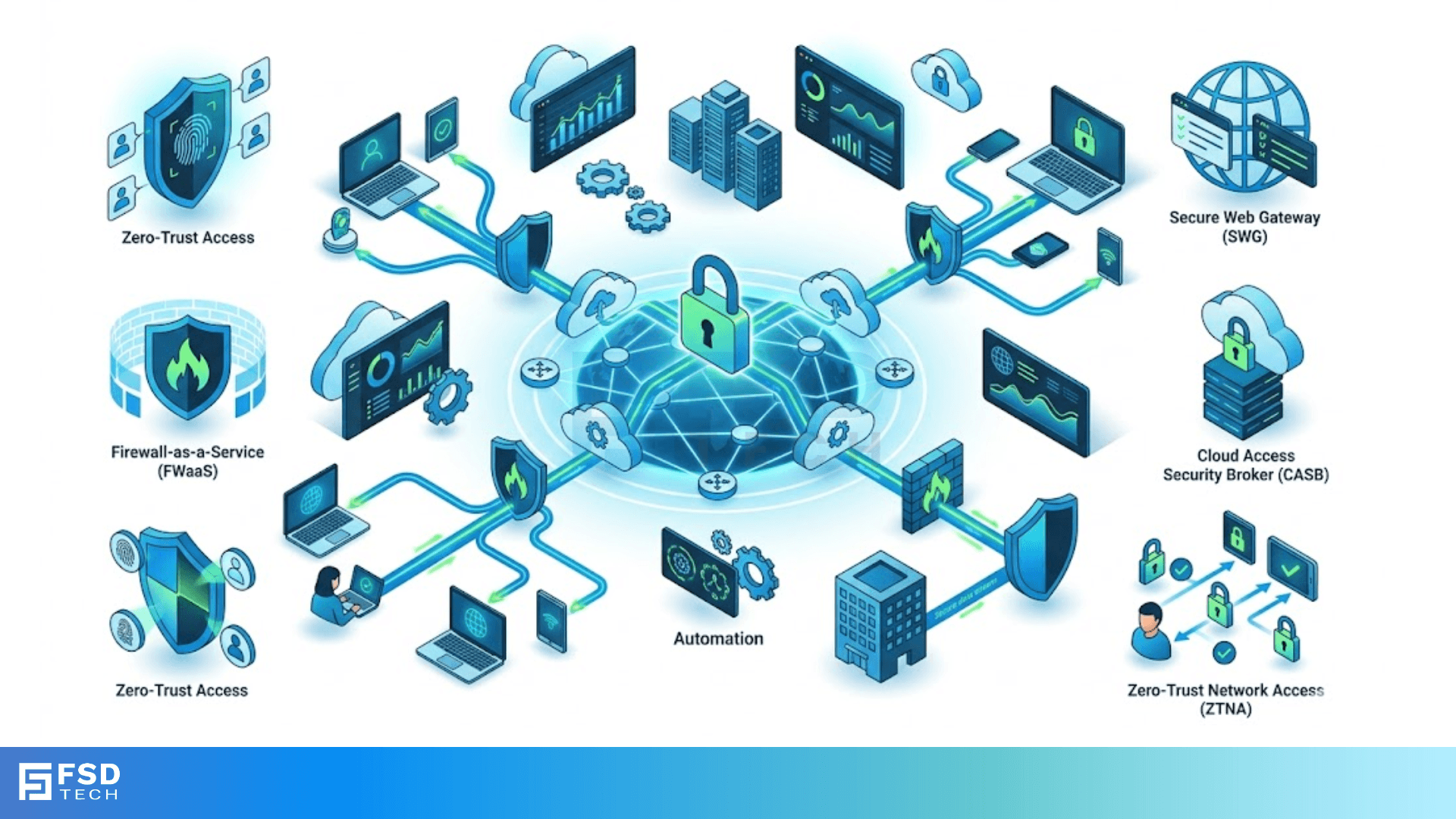
To really understand Security Service Edge, you need to know the four main tools it uses. These work together to create a "shield" around your business.
1. Zero Trust Network Access (ZTNA)
This tool follows one simple rule: trust no one. Even if you have the right password, ZTNA checks your identity and your device before letting you in. It’s the ultimate way to stop hackers from moving through your network.
2. Secure Web Gateway (SWG)
Think of this as a smart filter for the internet. It stops your employees from accidentally visiting dangerous sites. It also blocks viruses before they even reach your laptop.
3. Cloud Access Security Broker (CASB)
Do you know where your data goes when it's in Salesforce or Dropbox? CASB does. It makes sure your sensitive files don't end up in the wrong hands while they are in the cloud.
4. Firewall as a Service (FWaaS)
This is a powerful firewall that lives in the cloud. It inspects all your traffic to block attacks, no matter where you are working. You don't need to buy any more heavy hardware for your branch offices.
Every business has different needs, but Security Service Edge is flexible enough for everyone. Let’s look at two big examples.
Manufacturing and Industry 4.0
In my experience, factories are the hardest to secure. They use old machines that weren't built for the internet. SSE helps by creating a secure "tunnel" for these devices. It protects smart factories from cyberattacks that could stop production.
Retail and Hospitality
Retailers often have hundreds of small shops. Managing a firewall at every store is a nightmare. With SSE, they can manage security for all stores from one screen. It also keeps guest Wi-Fi separate from the credit card machines to stay safe.
Also Read: Predictive Maintenance Logic and Systems: Smart Repair
You might hear these two terms used a lot. Here’s the shortcut:
If you already have a good way to move data, you might just need SSE. But if you want to fix your slow network and your security at the same time, SASE is the way to go.
The world isn't going back to the old way of working. Most data is now outside the enterprise. If you keep using old tools, you'll spend more money and get less protection.
To be honest, switching to Security Service Edge is about more than just tech. It’s about giving your team the freedom to work safely from anywhere. It's about making your business agile enough to handle whatever comes next.
Are you ready to stop fighting with point solutions and start growing?
The shift to Security Service Edge is the most logical step for any growing business. We've seen how it simplifies complex networks and provides better protection than old-school tools. At Cato Networks, we focus on making your journey to the cloud as smooth as possible. We value your time and your safety, ensuring your team stays connected and your data stays private. Let's build a faster, safer future together.
Contact our Team for Better Solution
It stands for Security Service Edge. It is a cloud-based approach to network security.
Yes. Traditional VPNs are often slow and don't provide the "Zero Trust" protection that SSE offers.
Not at all. Since it's cloud-native, you can often turn it on without installing new hardware.
You save by not buying, shipping, and fixing physical security boxes at every location.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts