.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
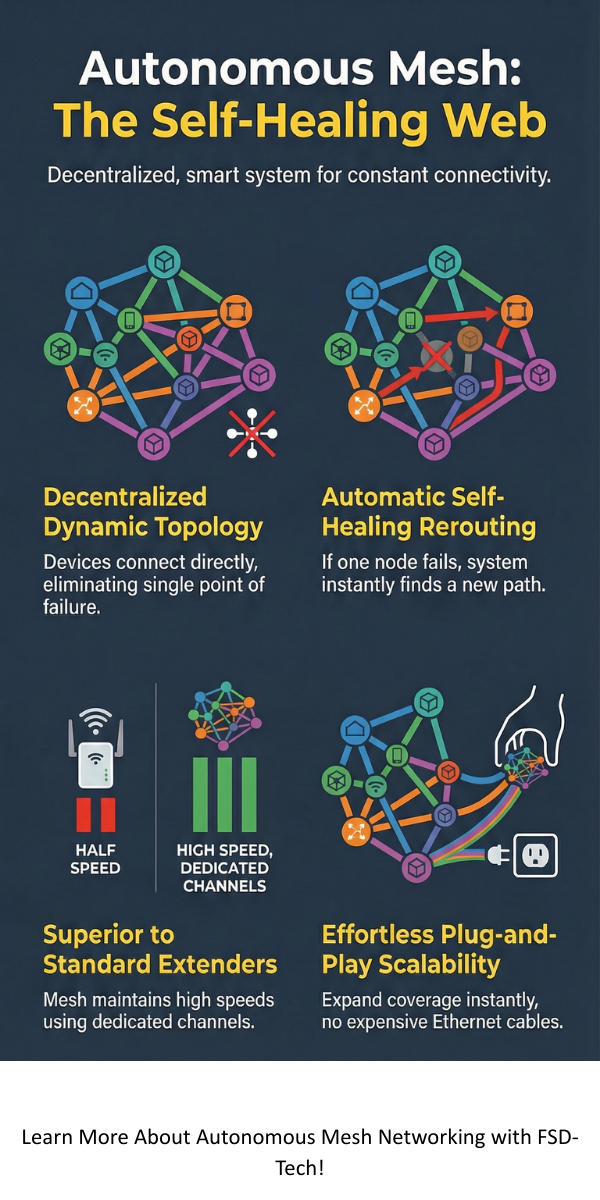
Autonomous Mesh Networking is changing how we think about staying connected in tough spots. Imagine a Wi-Fi network that doesn't just sit there but actually "thinks" and fixes itself when things go wrong. Most of us are used to standard routers, but those have a single point of failure. If the main hub dies, the whole house goes dark.
Here is the thing: what if the network could rebuild itself on the fly? That is the magic of an autonomous system. It is a web of devices that talk to each other directly. They don't need a central boss to tell them what to do. In this guide, we'll look at how these smart webs work and why they are the future of industrial and home internet.
To be honest, the term sounds more complex than it is. At its core, Autonomous Mesh Networking is a local network topology where nodes (devices like routers or sensors) connect directly and dynamically. They cooperate with one another to efficiently route data to and from users.
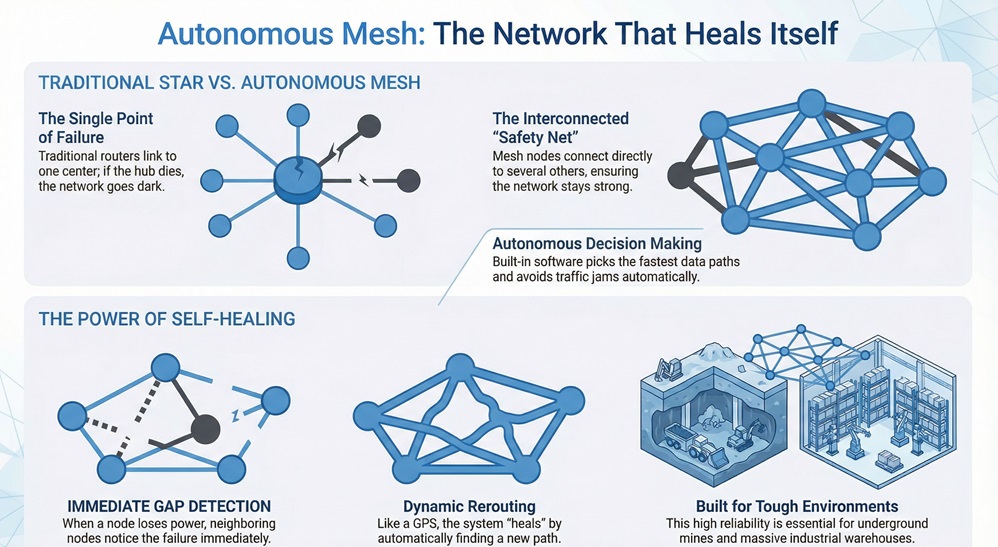
Unlike a star topology where everything links to one center, a mesh is like a safety net. Every knot in the net is connected to several others. If one knot breaks, the rest of the net stays strong. In an autonomous setup, the software inside these nodes makes decisions without human help. It picks the fastest path for your data and avoids traffic jams automatically.
Have you ever had your internet cut out because a cord got loose? In a mesh system, if one node loses power, the neighboring nodes notice it immediately. They "heal" the gap by finding a new path. It’s like a GPS rerouting you around a car accident. This makes Autonomous Mesh Networking incredibly reliable for places like underground mines or massive warehouses.
When we talk about Autonomous Mesh Networking, we have to mention standards like 802.11s. This is the "language" that allows different devices to form a mesh. We have all been there—trying to get two different brands of tech to talk to each other is usually a nightmare. These standards make it possible.
It means your connection stays stable even if you move from the living room to the backyard. The nodes are constantly negotiating behind the scenes to give you the best signal.
Also Read: Mesh Architecture: How to Decentralize Your Data
Autonomous Mesh Networking (or AMN) solves the "dead zone" problem. In my view, traditional extenders are a waste of time because they cut your speed in half. A true mesh keeps the speed high because it uses dedicated channels for the nodes to talk to each other.
Picture this: A disaster hits a city, and the cell towers go down. How do rescuers talk to each other? They can drop small mesh nodes every few hundred feet. Within seconds, an Autonomous Mesh Networking web forms. It creates a private communication bubble without needing any existing infrastructure.
In large factories, moving robots need constant contact with a server. As a robot moves, it "hands off" its connection from one mesh node to the next. This happens in milliseconds. If a forklift blocks a signal, the mesh finds a way around it. It is roughly the same tech used in self-driving cars to talk to each other on the road.
Also Read: Serverless Networking: Understand Cloud Connectivity
Now, I’m not saying it’s perfect. No tech is. One big hurdle for Autonomous Mesh Networking is "latency." Because data might have to "hop" through three or four nodes to reach the internet, it can take a tiny bit longer.
Also, the more nodes you add, the more "noise" or interference you might get. That’s why the "autonomous" part is so vital. The system must be smart enough to manage these frequencies so they don't drown each other out.
We've seen how connectivity has moved from messy wires to smart, invisible webs. At our company, we believe that staying connected shouldn't be a struggle. We focus on building tools that are simple, reliable, and "human-first." Whether you are setting up a smart home or a smart factory, Autonomous Mesh Networking is the bridge to a more reliable digital world. We're here to help you cross it.
Yes, absolutely. Extenders create a second network that slows you down. A mesh keeps everything on one seamless network with better speed.
Not necessarily. Many nodes are designed to be low-power, especially those used in "Internet of Things" (IoT) sensors.
You can, but it is best to wire your console to a node via Ethernet for the lowest possible lag.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts