.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
%20in%20Cato-01.jpg&w=3840&q=75)
Managing who can access what and with how much privilege—is a cornerstone of secure operations in any IT environment. To be honest, most security breaches don't happen because of a fancy hack; they happen because someone had permissions they didn't actually need.
With Cato Networks, Role-Based Access Control (RBAC) allows IT teams to enforce least-privilege access across administrators, service providers, and auditors. This ensures operational security and compliance without slowing down your workflow.
This guide walks through the RBAC implementation steps in the updated Cato Management Application (CMA), outlines real-world use cases, and offers tips for structuring access based on team roles.
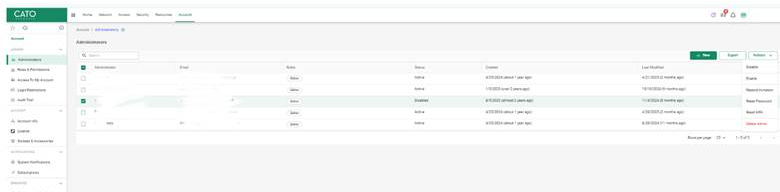
In the latest version of Cato’s Management Application:
Here, you’ll see a dropdown for selecting predefined roles or customizing access.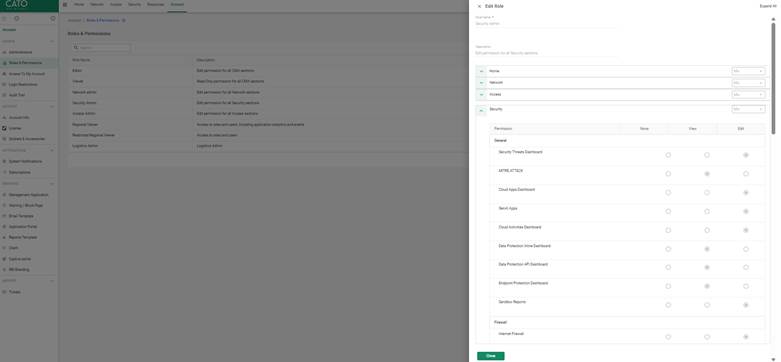
As of the latest release, Cato supports the following built-in roles:
Each role determines what tabs, data, and actions are visible and executable.
Also Read: Gain Real-Time Endpoint Intelligence with the Cato Device Dashboard
Use the following table to align user roles with IT roles:
| Team Member | Suggested Role | Justification |
| CISO / Compliance | Viewer | Needs audit access, not modification rights |
| Network Engineer | Network Admin | Full access to topology, rules, routing |
| Security Analyst | Security Admin | Manage threat dashboard, FWaaS, policies |
| MSP Technician | Custom Role | Limit to specific clients or regions |
| Tier 1 Support | Viewer or Custom | Access to logs, alerts—but no policy changes |
Let’s say you manage an internal IT team for a regional office. You want your Tier 2 engineer to troubleshoot firewall rules but not modify WAN configurations.
Steps:
This setup allows engineers to remain effective without overexposing critical infrastructure settings.
Also Read: Cato SASE Implementation Roadmap 2025: A Step-by-Step Guide
RBAC in Cato Networks isn't a "set it and forget it" task. To keep your environment secure, you need a bit of ongoing hygiene. Here's what I recommend to my clients:
RBAC in Cato Networks ensures only the right people have access to the right controls—no more, no less. It’s about building a "trust but verify" environment that scales with your company. Ready to tighten up your perimeter? Start structuring your access tiers today in your Cato CMA.
At our core, we believe that security should be simple, not a burden. We are committed to helping our clients achieve a seamless, secure connection for every user, on any device, everywhere.
Contact our Cato SASE Experts today
Yes, you can toggle individual permissions for a Custom Role during user creation.
Yes. You can edit user roles anytime via the User Management tab.
Yes, all user actions are logged in the Audit Trail for review.
Not directly. But you can control access scope via Custom Role and filtering policies.
MFA is user-based. You can enforce it during account setup regardless of role.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts