.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

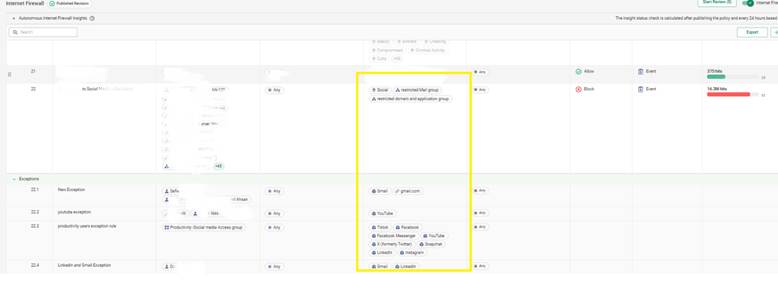
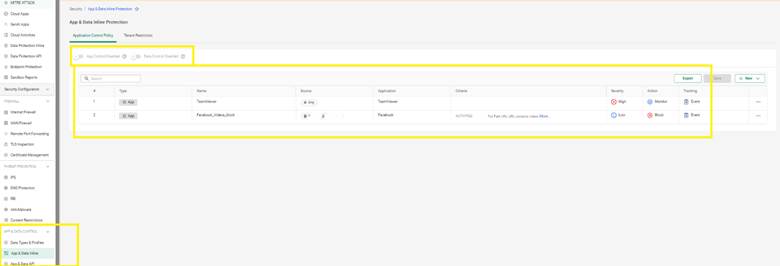
In today's world of hybrid work, you've likely seen how messy corporate networks can get. Between shadow IT and security risks, knowing exactly what runs on your WAN is a massive headache. Cato Application Control acts as your digital gatekeeper, offering a clear way to manage user behavior without the guesswork.
To be honest, most IT teams struggle because they can't see what they're trying to block. In my experience, the secret isn't just blocking everything—it's about granular visibility. The updated Cato Management Application (CMA) makes this easier than ever. We aren't just talking about simple port blocking; we're talking about identifying thousands of apps in real-time.
Are you tired of wondering which "productivity" tools are actually draining your bandwidth? Let's dive into how you can take back control of your network.
Application Control allows you to:
This feature is available for all customers with Threat Prevention enabled.
Also Read: Strategies to Eliminate Network Downtime with Cato SASE’s Reliable Global Backbone
Let’s say your compliance policy prohibits the use of personal file-sharing platforms like Dropbox or WeTransfer, but you still want to allow corporate OneDrive.
Solution:
This keeps your file policies clean while enabling visibility on violations.
Also Read: Cato SASE and DNS Security: Preventing and Mitigating DNS-Based Attacks
Monitor enforcement success and violations using:
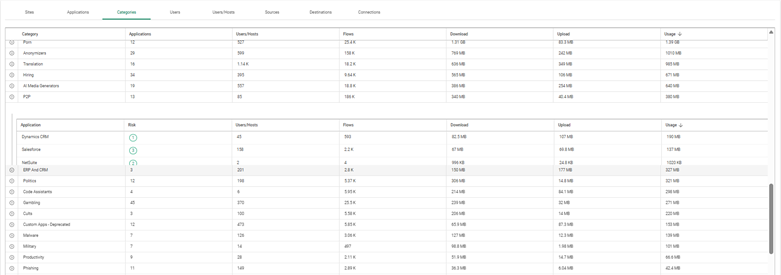
Use this data to:
So, this is how Cato Application Control empowers your IT team to manage the complexities of modern network traffic. It is nothing but a powerful tool to ensure your security matches the speed of your business. By moving beyond simple port blocking and embracing Layer 7 visibility, you create a safer, more efficient environment for everyone.
At our core, we believe that security should be a business enabler, not a roadblock. We focus on providing tools that are easy to use yet powerful enough to protect your most valuable data.
With Cato Application Control, your IT team can effectively strike the balance between enabling productivity and enforcing security. Start with a few high-impact policies and evolve them as your network visibility improves. Click Here To Know More
No, but enabling TLS inspection improves classification accuracy.
Yes, but only when Cato’s DLP (Data Loss Prevention) is enabled.
Analytics data is near real-time; logs are updated every few minutes.
Yes. Rules apply to all users connected via the Cato Client.
Yes. You can defin

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts