.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Cyberattacks have evolved well beyond what legacy firewalls were designed to handle. Ransomware dropper payloads, DNS tunneling, encrypted C2 (command-and-control) channels, and zero-day exploits now routinely bypass perimeter-only defenses — leaving organizations exposed.
Cato SASE (Secure Access Service Edge) takes a fundamentally different approach. Rather than bolting security onto the network edge, Cato integrates multi-layered threat prevention natively into its global private backbone — enforcing policy inline, at wire speed, without latency trade-offs.
This guide covers everything you need to know to configure, tune, and monitor Cato SASE threat prevention policies in 2026 — from IPS and Anti-Malware to DNS Security, TLS Inspection, and Managed Threat Intelligence.
Cato's security stack operates across all traffic — WAN and internet — through five integrated inspection engines:
Application- and identity-aware access controls that go beyond port/protocol rules. NGFW enforces who can access what, based on user identity, device posture, and application context.
Cato IPS detects and blocks exploits, known vulnerabilities, protocol tunneling, stealth protocols, and anomalous behavior — in real time and inline. It covers WAN, inbound, and outbound traffic simultaneously.
Combines cloud-based signature databases with behavioral heuristics to detect and block malware, ransomware droppers, and file-based attacks at the point of entry — before execution.
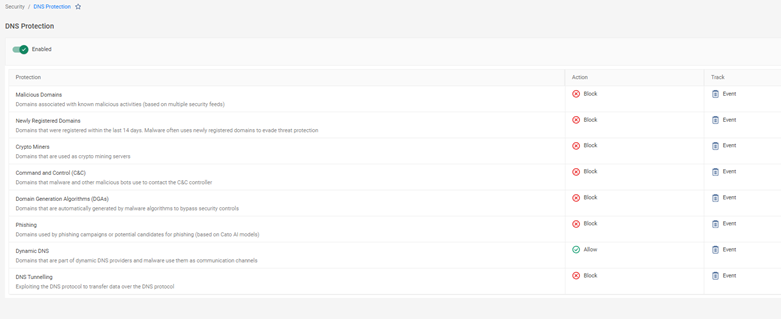
Blocks malicious DNS queries, stops phishing domain lookups, restricts newly registered domains, and supports DNS sinkholing to immediately identify compromised hosts. This is one of the most underutilized — yet highly effective — threat prevention controls available.
Up to 95% of enterprise traffic is now encrypted. Without TLS inspection, IPS and Anti-Malware are effectively blind. Cato decrypts, inspects, and re-encrypts traffic inline — with no detour to a separate proxy appliance.
Key advantage: All five engines operate in a single-pass architecture. There's no backhauling, no chained appliances, and no noticeable latency impact.
What makes Cato's prevention effective at scale is the Managed Threat Intelligence platform feeding each engine continuously.
| MTI Metric | Value |
|---|---|
| Global intelligence sources | ~250 |
| Total IOCs tracked | ~20 million |
| False positives filtered | ~10% |
| Validated IOCs enforced | ~18 million |
| Update frequency | Every ~3 hours |
MTI feeds directly into IPS signatures, DNS blocklists, Anti-Malware definitions, and the XDR (Extended Detection and Response) correlation engine. Unlike static signature updates on traditional appliances, this is a living, continuously tuned intelligence feed — with no manual intervention required.
Also Read: Auto-Adaptive Threat Prevention: How SASE Stops Modern Cyberattacks
Cato's threat prevention is profile-driven, meaning each site, remote user group, or socket can inherit a tailored prevention profile. This gives security teams granular control without creating policy sprawl.
Step 1: In the Cato Management Application, navigate to Security → Threat Prevention.
Step 2: Select an existing Prevention Profile or create a new one.
Step 3: Toggle the relevant inspection engines:
Step 4: Set enforcement actions per engine:
Step 5: Configure logging preferences for blocked and allowed events.
Step 6: Apply the profile to the appropriate sites, user groups, or individual sockets.
Pro tip: Use separate profiles for headquarters and datacenters (strict) vs. branch offices (balanced). This prevents over-blocking at critical sites while maintaining strong protection everywhere else.
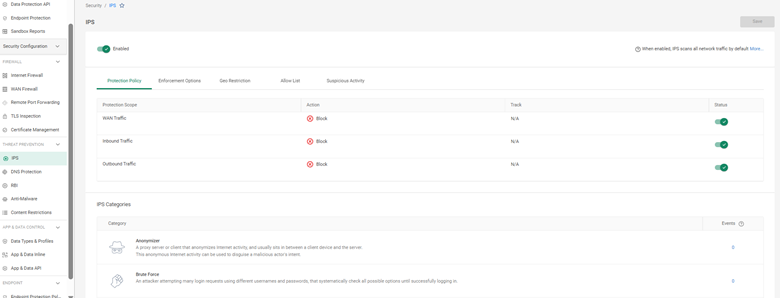
Sometimes, legitimate applications may trigger false positives. To handle this:
Cato’s IPS policy includes DNS protections for advanced control:
Also Read: Vendor Consolidation: Why SASE is the Future of IT
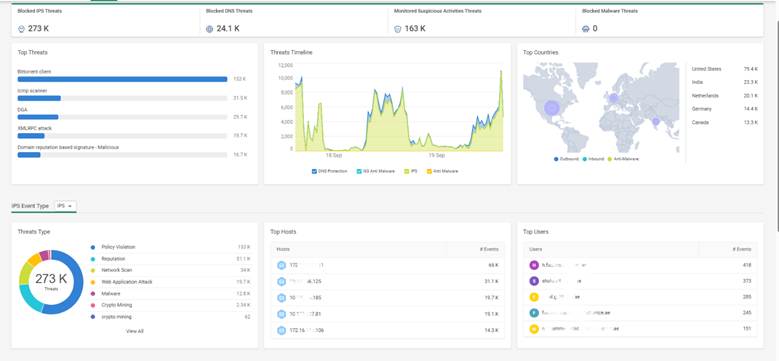
Cato provides detailed visibility into all blocked or allowed threats via:
A financial services firm in Dubai deployed Cato SASE with IPS + Anti-Malware + DNS Security enabled. Within days:
The SOC team used Threat Analytics to review all blocked attempts and reported zero successful breaches.
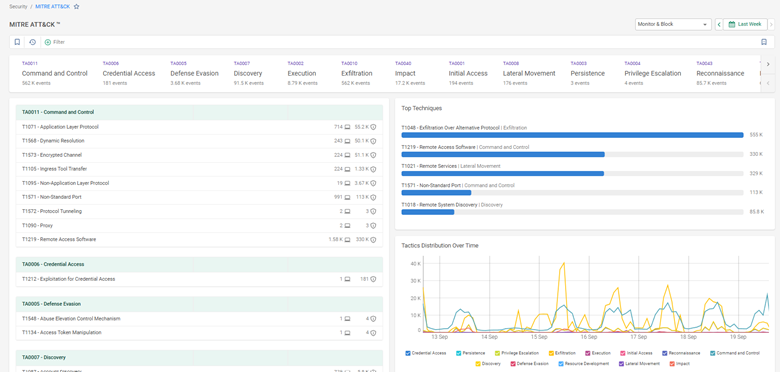
Cato's threat prevention maps directly to MITRE ATT&CK tactics, including:
| MITRE Tactic | Cato Control |
|---|---|
| Initial Access | IPS (exploit blocking), Anti-Malware |
| Execution | Anti-Malware (dropper prevention) |
| Command & Control | DNS Security (sinkholing), IPS (C2 signatures) |
| Exfiltration | DNS tunneling detection, TLS Inspection |
| Lateral Movement | WAN IPS, NGFW |
| Credential Access | IPS (brute force protection) |
Cato SASE delivers enterprise-grade threat prevention through a tightly integrated stack — IPS, Anti-Malware, DNS Security, TLS Inspection, and Managed Threat Intelligence — all enforced inline across every traffic flow without appliance overhead. When configured correctly with tiered profiles, targeted exceptions, and active monitoring, it provides the layered defense modern networks require against ransomware, C2 traffic, and zero-day exploits.
Book a free consultation with our experts to explore how Cato’s IPS, DNS Security, and TLS inspection can safeguard your network.

Cato ingests ~250 sources, totaling ~20 million IOCs. After filtering false positives, ~18 million validated IOCs are enforced, updated automatically every ~3 hours.
Yes. IPS can be configured to alert without blocking, useful for testing before enforcement.
When a domain is sinkholed, the malicious query resolves to an internal IP, enabling administrators to trace the compromised host and respond quickly.
You can allow trusted domains, file hashes, or applications in the Anti-Malware policy. Exceptions should be reviewed regularly to avoid exposure.
Yes. TLS inspection enables detection of hidden exploits, malware downloads, and stealth tunneling protocols inside encrypted traffic.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts