.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
%20in%20Cato.png&w=3840&q=75)
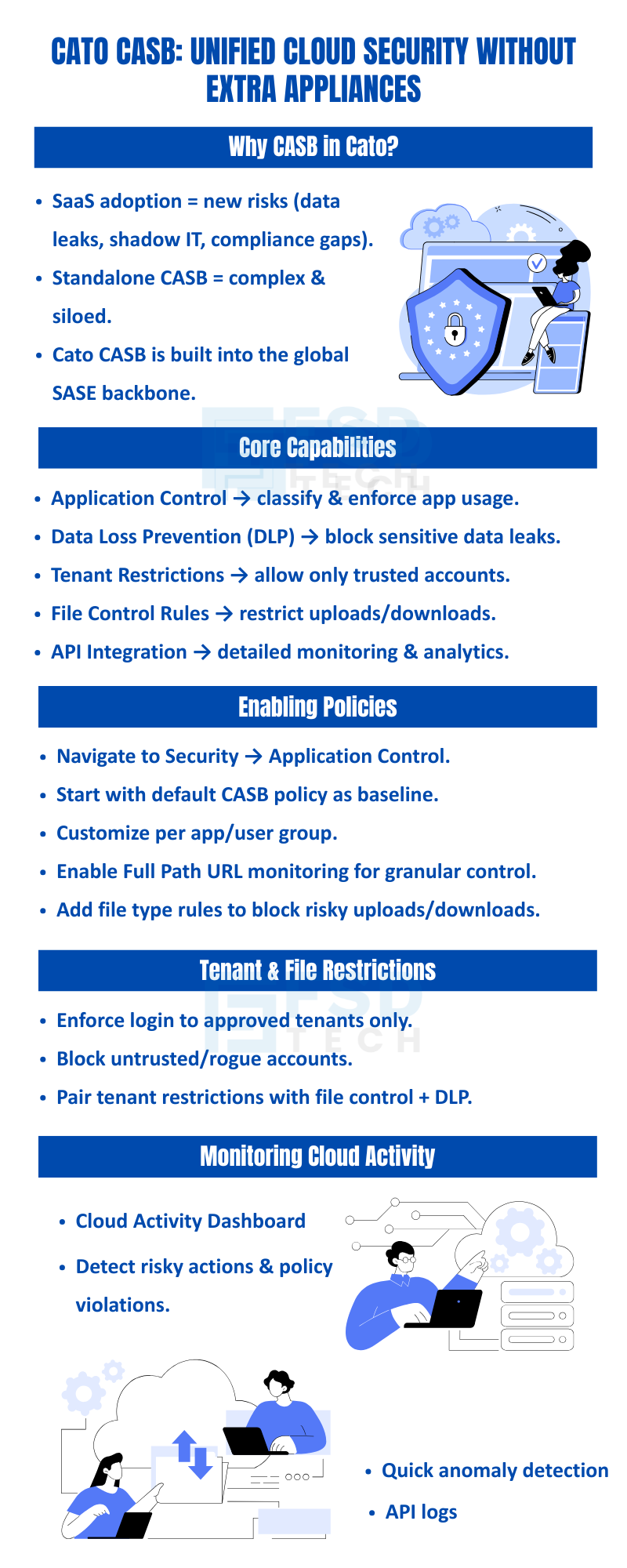
The average enterprise now uses over 130 SaaS applications. Each one is a potential data leak, a rogue access point, or a compliance gap — and traditional security tools weren't built to handle them.
Firewalls don't understand SaaS context. VPNs create a false sense of perimeter security. Standalone CASB appliances add cost, complexity, and yet another management console to a stack that's already too fragmented.
Cato's Cloud Access Security Broker (CASB) takes a different approach entirely. Built natively into the Cato SASE platform and enforced inline across the global backbone, it gives security teams unified visibility and granular policy control over every SaaS interaction — without bolting on additional hardware or agents.
This guide walks through exactly how to configure Cato CASB in 2025: from enabling application control policies and enforcing tenant restrictions to applying DLP rules, monitoring cloud activity, and integrating API-level visibility.
A Cloud Access Security Broker sits between users and cloud applications, enforcing security policies, monitoring activity, and preventing sensitive data from leaving the organization through SaaS channels.
What makes Cato's implementation different from traditional CASB products is where it lives. Rather than operating as a standalone proxy or requiring API-only integration, Cato CASB is embedded natively into the Cato SASE platform — enforced at the same PoP (Point of Presence) that handles all other traffic inspection, including firewall, IPS, and TLS decryption.
This means:
| Capability | What It Does |
|---|---|
| Application Control | Identify, classify, and enforce policies on cloud app usage |
| Data Loss Prevention (DLP) | Block sensitive data from leaving via SaaS uploads or sharing |
| Tenant Restrictions | Limit users to approved organizational accounts only |
| File Control Rules | Restrict upload/download of specific file types or categories |
| API Activity Monitoring | Track user actions, logins, and file events via app APIs |
| Cloud Activity Dashboard | Real-time visibility into SaaS usage across sites and users |
Application control is the foundation of Cato CASB. It determines which applications users can access, under what conditions, and with what level of inspection.
In the Cato Management Application, navigate to Security → Application Control.
Cato provides a recommended baseline CASB policy covering common SaaS categories. This is the fastest way to establish coverage without starting from scratch. Review the default rules before customizing.
Layer on specific rules for high-priority applications — such as Salesforce, Microsoft 365, Google Workspace, or Slack — and scope them to relevant user groups or departments. For example, you might allow full access for IT but restrict uploads for contractors.
This is a critical setting that many teams overlook. Full Path URL monitoring allows Cato to distinguish between:
Without it, policies apply only at the domain level — far too broad for meaningful SaaS control.
Define what types of files can be uploaded or downloaded across specific applications. Common configurations include:
Before pushing to enforcement, run policies in monitor mode to validate behavior against real traffic patterns. Promote to block mode once false positives are resolved.
Also Read: Global Private Backbone: Why Your Business Needs It?
One of the most common SaaS security gaps is tenant sprawl — users accessing personal or unauthorized versions of legitimate applications. An employee logging into their personal Google Drive or a contractor using an unapproved Dropbox account bypasses every corporate data control you have.
Cato CASB addresses this through tenant restrictions, which enforce that users can only authenticate to approved organizational accounts within a given SaaS application.
Best practice: Pair tenant restrictions with file control policies. Restricting the tenant prevents lateral account movement, while file control prevents data transfer even within approved tenants.
Cato's DLP engine operates inline on SaaS traffic, scanning content in real time against configurable data classifiers. When sensitive content is detected in an upload, share, or API transaction, policy enforcement triggers immediately.
Also Read: SASE Point of Presence (PoP): The Heart of Cloud-Native Networking
Configuring policies is only half the job. Cato CASB provides two primary layers of ongoing visibility:
Navigate to Analytics → Cloud Activity for a real-time overview of:
This dashboard is particularly useful for security operations teams during periodic access reviews and for identifying applications that should be added to formal policy coverage.
For high-risk or business-critical applications, Cato supports direct API integration with major SaaS platforms. This provides event-level telemetry beyond what traffic inspection alone can surface — including:
Integration tip: Forward Cato cloud activity logs to your SIEM (Splunk, Microsoft Sentinel, Chronicle, etc.) for correlation with endpoint and identity data. This creates a complete chain of custody for SaaS-related incidents.
A UAE-based financial firm used Cato CASB to protect its Salesforce and Office 365 environment:
1. Start with the default CASB policy, then customize. The recommended baseline covers the most common risk scenarios. Use it as your starting point rather than building from scratch — it accelerates deployment and ensures no critical category is missed.
2. Enable Full Path URL monitoring from day one. Domain-level visibility is insufficient for modern SaaS security. Full path monitoring is what unlocks tenant-level and feature-level control.
3. Pair tenant restrictions with file control and DLP. Each control addresses a different attack vector. Together, they create overlapping protection that's much harder to bypass.
4. Deploy DLP and file control in Alert mode before Block. Baseline your environment before enforcing. Premature blocking of legitimate file transfers creates business disruption and erodes trust in the security program.
5. Use API monitoring for high-risk applications. Traffic inspection tells you what's moving. API monitoring tells you what's happening inside the application. Use both for sensitive platforms like Salesforce, Workday, or financial reporting tools.
6. Review tenant restriction lists with HR and IT quarterly. Organizational changes — new subsidiaries, M&A activity, contractor onboarding — can make previously approved tenants invalid or introduce new legitimate tenants that need whitelisting.
7. Audit DLP and file control rules periodically. Rules that made sense 12 months ago may block legitimate business workflows today. Quarterly reviews prevent the accumulation of exceptions and shadow workarounds.
8. Correlate cloud activity logs with your SIEM. Cato's cloud activity data becomes significantly more powerful when joined with endpoint, identity, and email telemetry in a centralized SIEM for threat hunting and compliance reporting.
Cato CASB delivers the SaaS visibility and control that modern enterprises need — integrated natively into the SASE platform rather than added as another appliance in an already complex stack. When configured correctly with application control policies, tenant restrictions, DLP rules, file controls, and API monitoring, it provides comprehensive protection against the most common SaaS-related data loss and account compromise scenarios.
For organizations in the GCC, UAE, and Africa markets that are scaling SaaS adoption rapidly while managing lean security teams, the operational simplicity of a single-platform approach is as important as the security outcome itself.
See CASB in Action —
Schedule a Free session with our specialists to explore how Cato CASB can secure your SaaS applications, enforce tenant restrictions, and prevent data loss in real time.
Yes. You can enforce tenant restrictions to allow only authorized accounts.
Cato CASB allows administrators to define file control rules for specific file types or categories.
Yes. Application Control via API enables tracking user actions, logins, and uploads/downloads.
No. Cato’s CASB is integrated into the SASE platform, eliminating the need for additional appliances.
The Cloud Activity Dashboard provides real-time analytics, showing app usage, policy violations, and top users.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts