.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

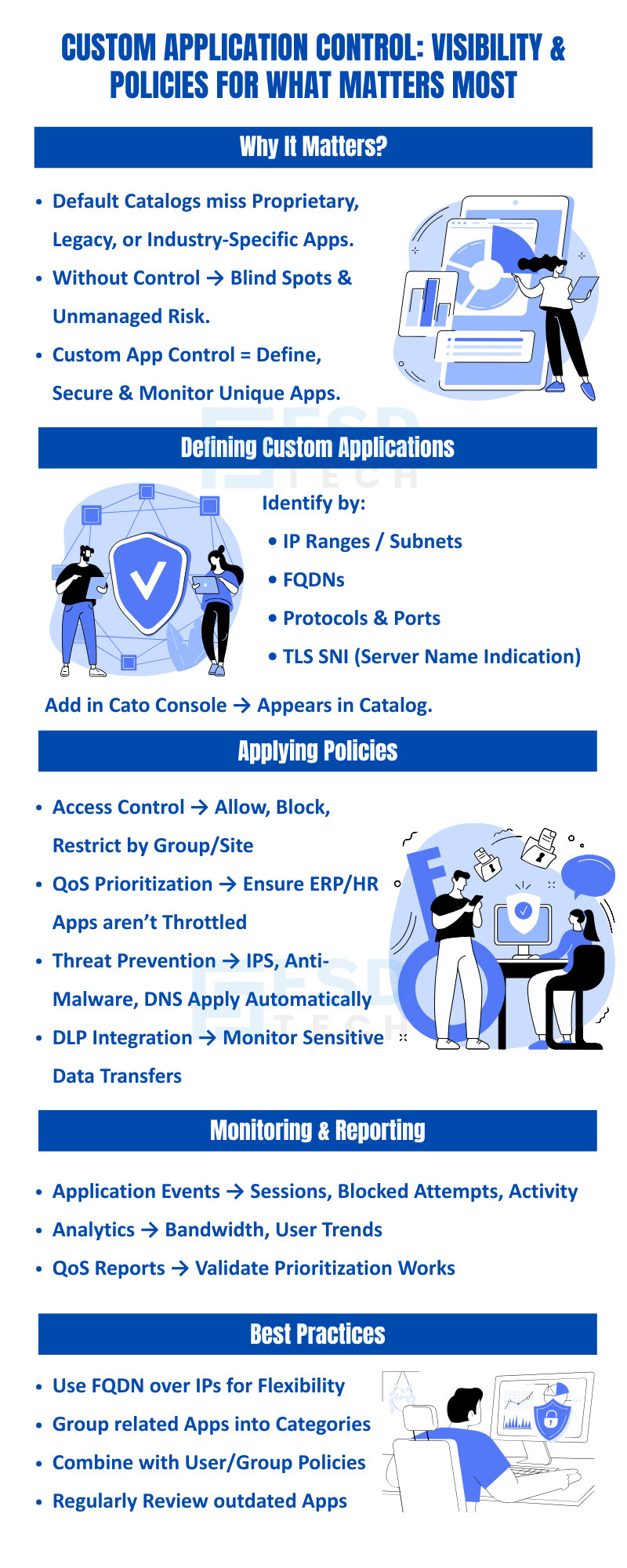
Every enterprise network carries a category of traffic that falls outside the scope of standard application libraries — proprietary business systems, internally developed portals, legacy industry-specific tools, custom APIs, and vertical applications built for specific operational requirements. These applications do not appear in predefined catalogs. They do not have pre-built policy templates. And without explicit definition in the security platform, they are effectively invisible to policy enforcement.
The consequences of that invisibility are significant and underappreciated. Bandwidth consumed by an unrecognized ERP system cannot be prioritized, meaning it competes equally with video streaming and social media traffic during peak hours. Data moving through an unrecognized internal HR portal cannot be subject to DLP inspection, meaning sensitive employee records can transit the network without any controls.
Sessions connecting to a custom manufacturing application cannot be inspected by IPS rules, leaving them exposed to exploitation without the protection applied to every other recognized application.
For organizations operating in the GCC region and across Africa — where proprietary enterprise systems, localized business applications, and industry-specific tools are particularly prevalent — this gap between what security platforms recognize by default and what organizations actually run is a practical security and operational challenge that demands a direct solution.
Cato SASE addresses this through custom application control: the ability to define any application not in the default catalog, apply the full Cato security and policy stack to it, and monitor its usage with the same depth available for predefined applications.
Cato's custom application control capability allows IT and security administrators to define applications that are not present in Cato's predefined application library, and then treat those applications as first-class citizens in the policy framework — subject to the same access controls, QoS prioritization, threat prevention inspection, DLP enforcement, and reporting capabilities available for any built-in application.
Once a custom application is defined, it integrates directly into the Cato Management Application's policy engine. It appears in the application catalog alongside predefined applications, can be referenced in firewall rules, QoS policies, and security profiles, and generates analytics data that appears in the same reporting interfaces used for all other application traffic.
The practical effect is that the boundary between "recognized" and "unrecognized" traffic disappears for the applications your organization defines. An internal ERP system running on a proprietary protocol becomes as visible and policy-manageable as Microsoft 365 or Salesforce. A custom API built by your development team becomes subject to DLP inspection and IPS threat detection. A legacy manufacturing application becomes a named entity in your security policy rather than an anonymous traffic flow.
This matters not just for security but for operational clarity. When every significant application your organization runs is named and defined in the policy platform, your security posture becomes auditable, your QoS configuration becomes purposeful, and your incident investigations become faster and more accurate.
Consult with us in just one tap
While Cato provides a comprehensive library of applications (cloud, SaaS, collaboration, productivity), enterprises often have unique needs:
Without the ability to define these apps, visibility is lost, and policies cannot be enforced. Custom application control solves this gap.
Also Read: How the Cato Client Becomes the Identity Anchor for Zero Trust Access
Custom applications can be defined based on multiple identifiers, including:
Note: Custom applications are descendants of matching predefined applications. The first matching firewall or network rule is applied to the custom or predefined application. If you want to apply the rule action for a specific application, make sure that this rule is placed above any other rule that contains matching predefined applications.
Once created, custom applications can be managed like any other app in Cato’s platform:
Note: Although Cato Networks continuously updates its predefined application and service list, in some cases, you may not find a commonly-used application/service for which you are searching. If this occurs, please open a support ticket so that Cato adds the application/service to the predefined list. While you are waiting for the predefined application, you can create the specific application/service as a custom application as a workaround until it is available in the Cato Management Application.
Also Read: Platforms, Countries, and Origin of Connection: Advanced Device Criteria in Cato Firewall
Administrators can track how custom applications are used via:
Note: The App Analytics page includes data for blocked apps. This is because the Point of Presence (PoP) allows the client device trying to access the app to send multiple packets to the PoP, so it can identify the app and apply the block rule. This request and response traffic between the client device and PoP is included in App Analytics data.
A construction company in the GCC region defined their custom ERP as a recognized app in Cato. With policies:
This provided full visibility, ensured compliance, and protected critical systems without deploying extra appliances.
Custom application control closes one of the most significant practical gaps between what enterprise security platforms recognize by default and what enterprise networks actually carry. For organizations running proprietary ERP systems, internally developed portals, legacy industry tools, or vertical-specific applications, the absence of custom application control means those applications operate outside the security policy framework — invisible to access controls, unprotected by threat prevention, unmonitored by DLP, and unmanaged by QoS.
Cato's custom application control capability brings those applications fully into the security framework without additional appliances, complex network changes, or application modifications. Once defined, a custom application receives the same depth of policy management, threat inspection, DLP coverage, and usage visibility as any predefined application in the Cato catalog.
For GCC and Africa enterprises where proprietary and industry-specific applications are particularly prevalent, this capability is not a niche feature — it is a foundational requirement for achieving the comprehensive visibility and consistent security posture that modern network environments demand.
Book a free consultation with our experts and explore how to configure, monitor, and secure your internal apps with Cato.
You can define by FQDN, IP ranges, protocols, or port numbers. TLS SNI is also supported for encrypted traffic.
Yes. Once created, they can be prioritized or deprioritized like built-in apps.
All defined apps are subject to IPS, DNS, and Anti-Malware rules. For example, if a custom app connects to a malicious domain, DNS protection will still block it.
Applications are individual definitions, while categories allow grouping multiple apps together for policy enforcement.
Yes. Cato’s DLP engine can monitor and control sensitive data transfer in both standard and custom applications.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts