.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
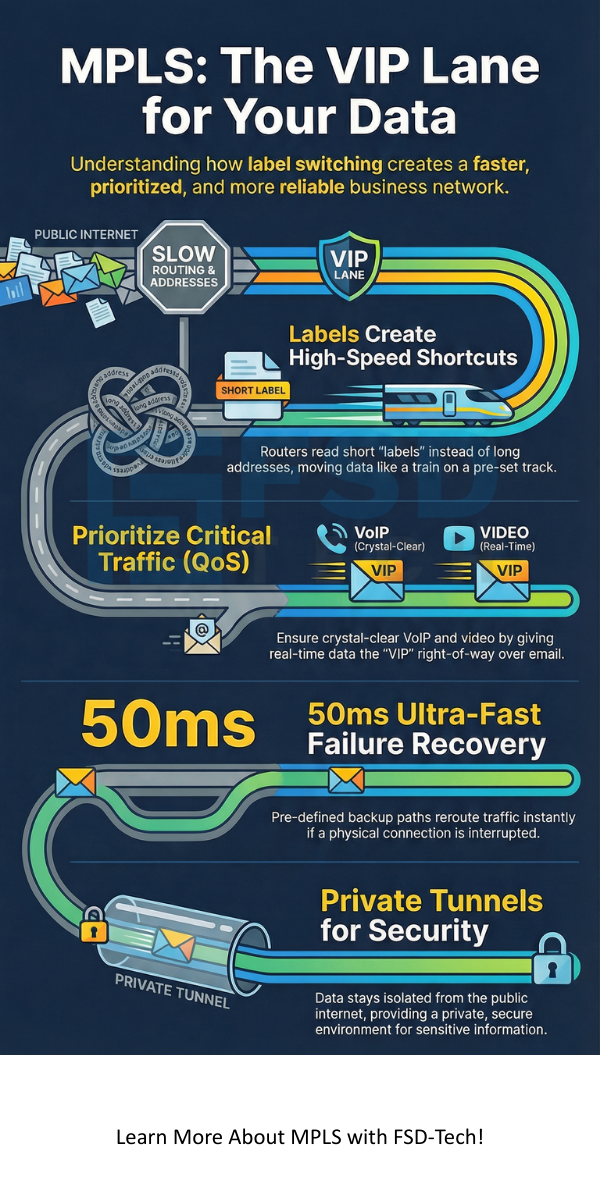
MPLS is a clever way to move data across a network faster than traditional methods. If you've ever wondered why some office connections feel snappier than a home Wi-Fi setup, the secret usually lies in how the routers talk to each other. Instead of looking at long, messy street addresses for every single packet of data, this system uses short "labels" to zip information to its destination.
Think of it like a VIP pass at a music festival. While everyone else waits in a long line for security to check their IDs, you just show your wristband and breeze through. But how does this actually work under the hood of a global enterprise network? And why do big companies still pay for it when high-speed internet is everywhere?
To be honest, the tech world loves to make things sound harder than they are. We’ve all been there—staring at a screen full of acronyms and feeling like we need a PhD just to understand a router. But here’s the thing: at its heart, this technology is just about making shortcuts.
Multi-Protocol Label Switching, or MPLS, is a routing technique that directs data from one node to the next based on short path labels rather than long network addresses. We call it "multi-protocol" because it doesn't care if your data is IP, Ethernet, or something older like ATM. It wraps them all up and sends them on their way.
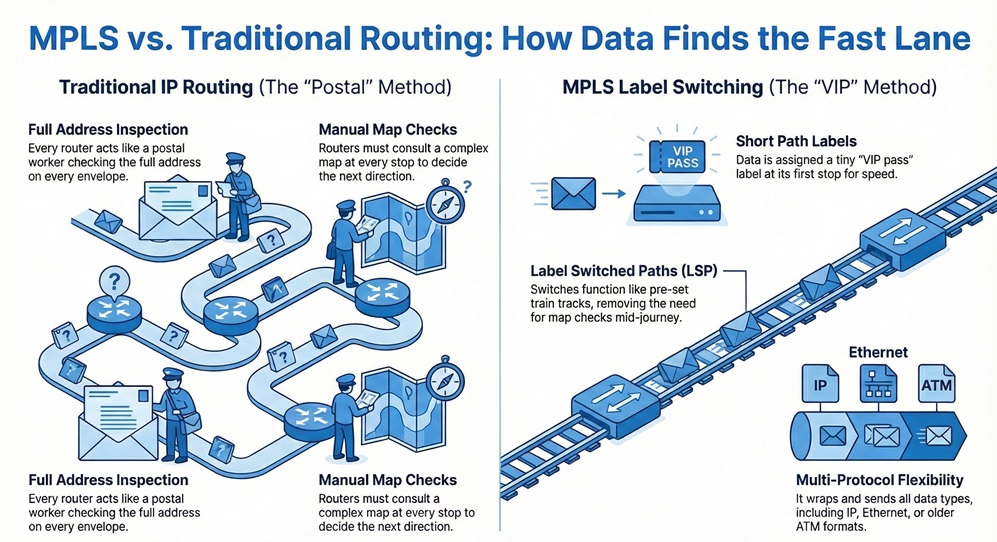
In a standard IP network, every router acts like a postal worker who has to look at the full address on an envelope, check a giant map, and decide where it goes next. This takes time. MPLS changes this by putting a "label" on the packet at the very first stop. From then on, every router along the path only looks at that tiny label.
When we use labels, we create a pre-set path through the network. This is known as a Label Switched Path (LSP). It’s like a train track. Once the train is on the track, the conductor doesn't have to check a map at every junction. The switches are already set.
In my view, this is the most efficient way to handle "real-time" data. If you're on a Zoom call or using a VoIP phone, you can't have packets arriving out of order or late. You'll get that annoying robot voice or a frozen screen. Labels ensure that those important packets follow the fastest, most reliable path every single time.
Now, let's discuss how a piece of data actually travels through this system. It involves three main types of routers that handle the heavy lifting.
Also Read: Infrastructure Monitoring: Your Guide to a Healthy Tech Stack
Sometimes, a packet might have more than one label. This is called a label stack. We use this for complex tasks like creating a Virtual Private Network (VPN). The top label tells the network how to get to the right office branch, while the inner label tells the office router which specific computer should get the data.
It is roughly like a Russian nesting doll. You open one layer to find the next instruction inside. This allows service providers to keep different customers' data completely separate, even though it's all traveling over the same physical wires.
You might be asking, "Why shouldn't I just use the regular internet?" That’s a fair question. While the public internet is cheap, it's also "best effort." That means your data competes with Netflix binging and cat videos.
Guaranteed Quality of Service (QoS)
One of the best things about MPLS is Quality of Service. We can tell the network that voice traffic is the most important, followed by video, and then email. If the network gets crowded, the email might slow down by a second, but your phone call will stay crystal clear.
Improved Uptime
Because the paths are pre-defined, the network can have a "backup" path ready to go. If a fiber optic cable gets cut by a construction crew (it happens more than you'd think!), the network can switch to the backup path in under 50 milliseconds. You won't even notice the blip.
Security and Privacy
Since this technology creates a private path, your data isn't mingling with the general public on the internet. It acts like a private tunnel. For banks or healthcare companies, this level of privacy is a must-have.
Also Read: What is WAN Optimization and Why Does Your Business Need It?
Lately, people are talking a lot about Software-Defined Wide Area Networking (SD-WAN). Some say it will kill the old label-switching way of doing things. In contrast, I think they actually work better together.
Many companies now use a "hybrid" approach. They use a private label-switched line for their most important office apps and cheap internet for guest Wi-Fi and basic web browsing.
To be honest, the terminology can get a bit thick. Let's break down a few LSI keywords you might see in technical manuals:
Fast-forward to today, and some critics say this tech is outdated. But we've all been there—trying to run a high-stakes business meeting over a shaky home connection. Reliability still matters.
While cloud apps like Office 365 or Salesforce have changed the game, the core need for a stable, low-latency backbone hasn't gone away. It’s not just about speed; it's about consistency. That is why most large hospitals, banks, and government agencies still rely on it.
At the end of the day, MPLS is about peace of mind. It’s for the business that can't afford a single minute of downtime or a glitchy customer call. While newer technologies offer more flexibility, the rock-solid nature of label switching keeps it at the top of the networking world.
At FSD-Tech, we believe in building networks that grow with you. Our team focuses on making sure your tech stays out of the way so you can focus on your clients. If you're tired of "best effort" and want a network that actually works, we're here to help.
No, it is a private network managed by a provider. The internet is a public "network of networks" with no single owner or performance guarantee.
Actually, it doesn't provide encryption by itself. It provides separation. If you need top-tier security, you usually run an encrypted tunnel (like IPsec) inside the labeled path.
You aren't just paying for the wire; you're paying for a Service Level Agreement (SLA). The provider guarantees it will work 99.9% of the time and fixes it fast if it breaks.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts