.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
For decades, enterprise networks were defined by a rigid, perimeter-based approach. The standard toolkit included MPLS circuits for reliable branch connectivity, on-premises firewalls for perimeter security, VPN concentrators for remote access, and a hub-and-spoke topology that funneled all traffic through a central data center. This model assumed that users, applications, and data were static and resided within the corporate perimeter.
In this environment, MPLS provided predictable, high-quality connections between sites, while firewalls enforced security at the network edge. VPNs extended access to remote users, but always through the same centralized control points. This architecture was manageable when employees worked from fixed offices and applications were hosted on-premises.
However, the world has changed. Cloud adoption, SaaS proliferation, and hybrid work have dissolved the traditional perimeter. Users now connect from anywhere, and applications live in multiple clouds. The legacy model, built for a static, centralized world, is now a barrier to agility and innovation.
The legacy approach is appliance-heavy and operationally fragmented . Each branch requires its own stack of hardware—firewalls, routers, WAN optimizers—leading to inconsistent security enforcement and complex management. Bringing a new site online means provisioning MPLS, shipping appliances, and configuring policies, often taking weeks or months.
Key operational pain points include:
As organizations expand globally, adopt cloud services, and support remote work, these challenges multiply. The legacy model cannot keep pace with the demands of a modern, distributed enterprise.
Cloud migration exposes the limitations of perimeter-based networking. Applications and data now reside in public clouds, SaaS platforms, and distributed data centers . Legacy networks, designed to route all traffic through a central hub, create bottlenecks and degrade performance for cloud-bound traffic.
For example, a user in Singapore accessing a SaaS application may have their traffic routed through a corporate data center in London for security inspection. This "hairpinning" adds latency, increases costs, and undermines the user experience.
The rise of hybrid and remote work has exposed the weaknesses of VPNs and perimeter-based security. VPNs were never designed for large-scale, always-on remote access. As more users connect from home or on the road, VPN concentrators become chokepoints, causing slowdowns and dropped connections.
Traditional security models grant broad access based on network location. Once authenticated, users often have access to more resources than necessary—a risky proposition in the age of phishing, ransomware, and insider threats.
Global expansion magnifies the challenges of legacy networking. Opening new branches requires shipping hardware, provisioning MPLS circuits, and configuring appliances at each location. This process is slow, costly, and difficult to scale. Managing hundreds of distributed firewalls and routers becomes a logistical nightmare, especially when IT resources are centralized or limited.
Also Read: Deep Dive into the Cato Device Inventory Page: Unified Asset Visibility for Cato SASE
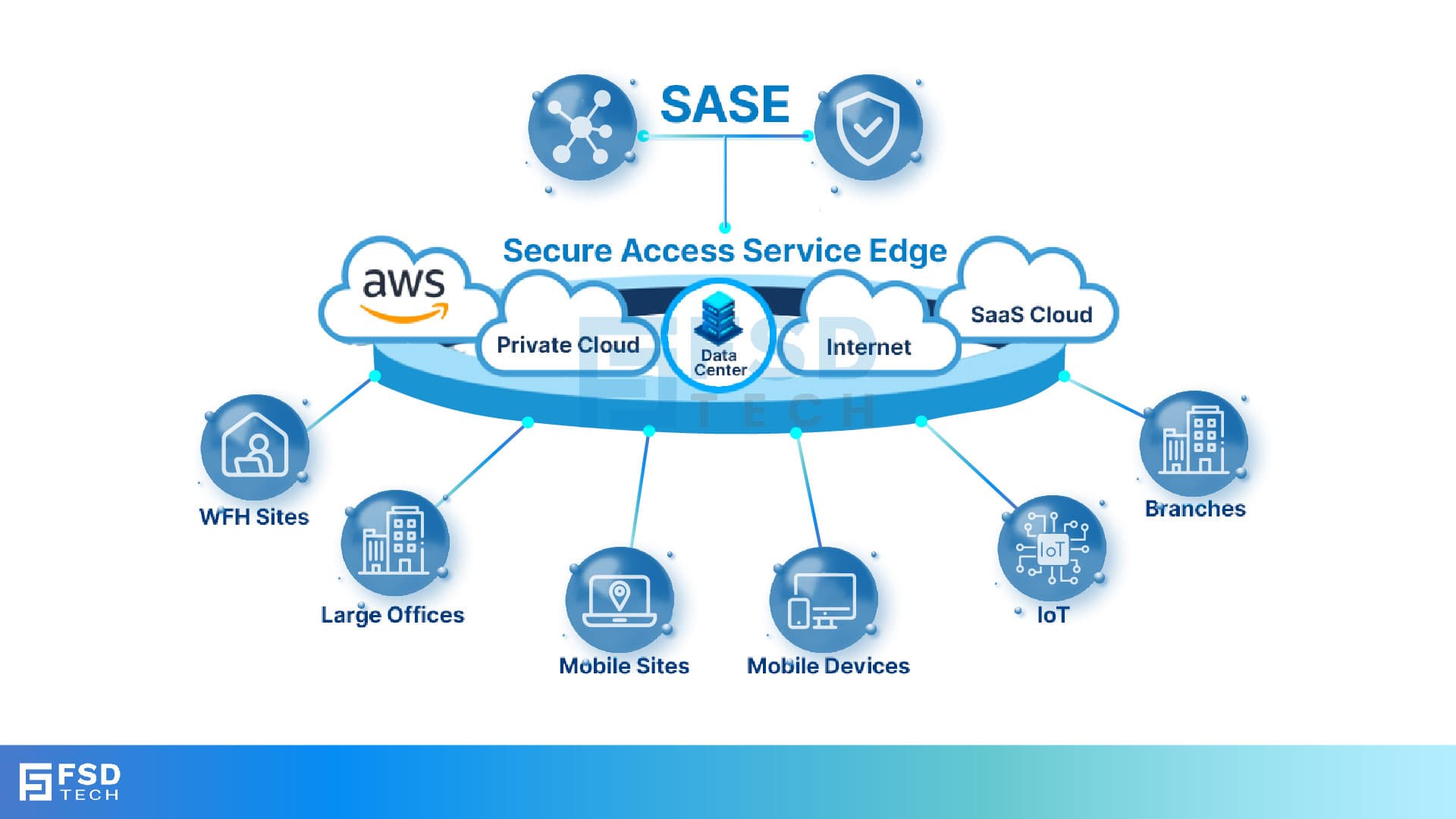
Secure Access Service Edge (SASE) is a cloud-native architecture that converges networking and security into a single, unified service delivered from the cloud. SASE is designed for a world where users, devices, and applications are everywhere.
Core SASE components include:
SASE platforms are cloud-native, globally distributed, and managed centrally , enabling organizations to enforce consistent policies, scale elastically, and support users and applications anywhere.
| Feature | Legacy Networking/Security | SASE (Cato Example) |
| Deployment Model | Appliance-driven, on-premises | Cloud-native, globally distributed |
| Security Integration | Fragmented, add-on | Native, unified |
| Policy Management | Decentralized, manual | Centralized, automated |
| User Experience | Latency-prone, inconsistent | Optimized, consistent |
| Agility | Static, slow to adapt | Dynamic, rapid onboarding |
| Scalability | Limited by hardware | Elastic, cloud-scale |
| Cost Structure | High CapEx, ongoing OpEx | Predictable, usage-based |
Also Read: Gain Real-Time Endpoint Intelligence with the Cato Device Dashboard
Cato Networks delivers a converged SASE platform that replaces the patchwork of MPLS, NGFW, VPN, and SD-WAN with a single, cloud-delivered service. All traffic—branch, remote, cloud, and mobile—flows through Cato’s global network of Points of Presence (PoPs) , where it is inspected, routed, and secured in real time.
Key benefits:
Unlike SD-WAN solutions that rely on the public internet, Cato operates a private global backbone connecting its PoPs. This backbone is engineered for low latency, high availability, and optimized routing, delivering MPLS-like performance without the cost or rigidity of legacy circuits.
Cato’s single-pass engine inspects traffic once for all security functions—firewall, threat prevention, data loss protection, and more. This approach reduces processing overhead, accelerates performance, and ensures that security is always enforced, regardless of where users connect.
A global retailer with over 300 stores worldwide faced mounting MPLS costs and inconsistent security enforcement. By adopting Cato’s SASE platform, they replaced MPLS with Cato’s private backbone, onboarded new sites in days (not weeks), and enforced uniform security policies across all locations. The result: lower costs, faster expansion, and reduced risk.
A financial services firm with 60% of its workforce remote struggled with VPN bottlenecks and security gaps. Cato enabled direct, secure access to cloud and on-premises applications for all users, regardless of location. Centralized policy enforcement and continuous verification ensured that every connection was secure, reducing the risk of breaches and improving user productivity.
A SaaS provider operating across AWS, Azure, and Google Cloud needed unified access and security controls. Cato’s platform provided a single pane of glass for managing policies, monitoring traffic, and enforcing compliance—eliminating the need for multiple firewall appliances and manual policy mapping.
Also Read: Cato SASE and DNS Security: Preventing and Mitigating DNS-Based Attacks
By consolidating networking and security into a single platform, Cato reduces the number of tools, vendors, and processes IT teams must manage. This leads to:
Cato’s cloud-native architecture enables organizations to adapt quickly to changing business needs:
Legacy networks—built on MPLS, hardware firewalls, and fragmented point solutions—are no longer viable for cloud-first, mobile-first enterprises. They are costly, complex, and ill-suited to the demands of a distributed, dynamic world.
Cato’s converged SASE architecture offers a strategic, future-proof alternative. By unifying networking and security in the cloud, Cato eliminates appliance sprawl, accelerates cloud adoption, and empowers IT leaders to deliver secure, high-performance connectivity to every user, everywhere.
For organizations seeking to modernize their networks, support hybrid work, and embrace the cloud with confidence, Cato represents the cleanest, most strategic path away from legacy sprawl—enabling agility, security, and scale for the digital era.
Contact our Cato SASE experts today
SASE integrates networking and security in a single cloud-native platform, whereas SD-WAN and VPNs address only connectivity. SASE provides unified security, centralized management, and better performance for distributed and mobile users.
Yes. SASE platforms like Cato use a private global backbone to deliver MPLS-like performance with greater flexibility and lower cost, eliminating the need for expensive, rigid MPLS circuits.
Cato delivers security as a cloud service, enforcing policies consistently regardless of user location, and uses Zero Trust principles for continuous verification.
SASE simplifies management by consolidating point solutions, automating policy enforcement, and reducing hardware dependencies, leading to faster deployments and lower operational overhead.
Cato’s single-pass engine inspects traffic once for all security functions, reducing latency and processing overhead. This ensures comprehensive protection without sacrificing user experience.
Centralized policy enforcement and unified logging make it easier to demonstrate compliance with regulatory requirements. Cato’s platform provides detailed reporting and continuous verification, simplifying audits.
Cato provides unified access and security controls across all cloud platforms and SaaS applications, eliminating the need for multiple firewall appliances and manual policy mapping.
Organizations typically see significant cost savings by eliminating MPLS circuits, reducing hardware purchases, and streamlining management. Cato’s predictable, usage-based pricing further simplifies budgeting.
New sites and users can be onboarded in days or even minutes, compared to the weeks or months required for legacy MPLS and appliance-based deployments.
Cato’s private global backbone optimizes routing and minimizes latency, delivering reliable application performance and a consistent user experience, regardless of location.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
share your thoughts