.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Long before cloud storage, artificial intelligence, or even ransomware became everyday words, IT professionals had a simple golden rule for protecting data: The 3-2-1 Backup Strategy.
It goes like this:
3 copies of your data
2 different types of storage
1 copy stored off-site
For years, this rule was the gold standard for everyone from small businesses to large corporations.
But in 2025, with new cyber threats and more businesses moving to the cloud, many people are asking: Is the 3-2-1 rule still enough?
Imagine all the valuable information your business relies on:
Now imagine losing it all in a single moment — because of a cyberattack, a hard drive crash, a flood, or even a simple mistake.
Long before cloud storage or fancy security tools, IT experts created a simple rule that could protect businesses from this kind of disaster. That rule is called the 3-2-1 backup strategy, and it’s still one of the smartest ways to keep your data safe.
The numbers stand for:
It’s that simple — but it’s powerful because it makes sure you always have a backup plan, even if something unexpected happens.
This means you should always have:
Why 3 copies?
If your main file gets corrupted and your first backup is damaged or missing, you still have the third copy as a safety net.
Don’t put all your eggs in one basket. If all your backups are stored on the same type of device, a single problem could wipe them all out.
For example:
Different storage types reduce the chance that one technical problem will destroy all your backups.
This means one backup copy should be stored in a different location from your main office.
Why? Because fires, floods, theft, or other disasters could destroy both your computer and your local backups at the same time.
An off-site copy could be:
The 3-2-1 rule has been around for decades because it works. It protects you from:
While the 3-2-1 rule is still strong, cyber threats have evolved. Ransomware now tries to find and destroy your backups before locking your main files.
That’s why many experts now recommend an upgraded version of the rule called 3-2-1-1-0.
Not sure if your current backup plan can withstand ransomware? Let our experts review your setup — free of cost. Click Here
Here’s what it means:
This modern version keeps the original logic of 3-2-1 but adds extra safety against modern threats like ransomware.
Vembu takes the traditional backup strategy and adds the tools needed for today’s environment:
Want to see how Vembu can make 3-2-1-1-0 effortless for your business? Book a free consultation slot today.
A design agency in Dubai used Vembu with a 3-2-1-1-0 setup. When a water leak destroyed their main office server, they restored all their files from an immutable off-site backup stored in the cloud. They didn’t lose a single file, and they were back in business within hours.
The 3-2-1 rule has stood the test of time, but 2025 demands a little extra protection. By adding immutability and verification, you’re not just making copies of your data — you’re making untouchable, reliable copies that can save your business in a crisis.
If your backup strategy is missing any part of 3-2-1-1-0, you’re at risk. Let’s set it up together with Vembu BDR Suite — get started today
The 3-2-1 backup rule is a time-tested safety plan for protecting your data from loss.
It says you should always have:
It’s like having your important documents:
Having just one copy is risky — if it’s lost, damaged, or stolen, you have nothing.
Two copies are better, but both could be in the same place and get destroyed together.
Three copies give you extra protection — even if one is damaged and another is corrupted, you still have a safe version to restore from.
This means you store your backups on different devices or platforms so one type of failure doesn’t wipe them all out.
For example:
It’s like keeping one copy of your house key in a key cabinet and another hidden in a safe — if one is lost, the other still works.
If all your copies are stored in your office, one incident (fire, water damage, theft, power surge) could destroy everything at once.
An off-site copy — like a cloud backup or a drive stored at another location — ensures your data is still safe if something happens to your main site.
It can, but only if your off-site backup is also well protected. If ransomware infects your systems, it could also damage backups that are always connected to the same network.
That’s why an upgraded version of the rule is better for 2025.
It’s the modern version of the 3-2-1 rule designed for today’s cyber threats. It adds:
This protects you even if hackers get into your systems and try to destroy every backup.
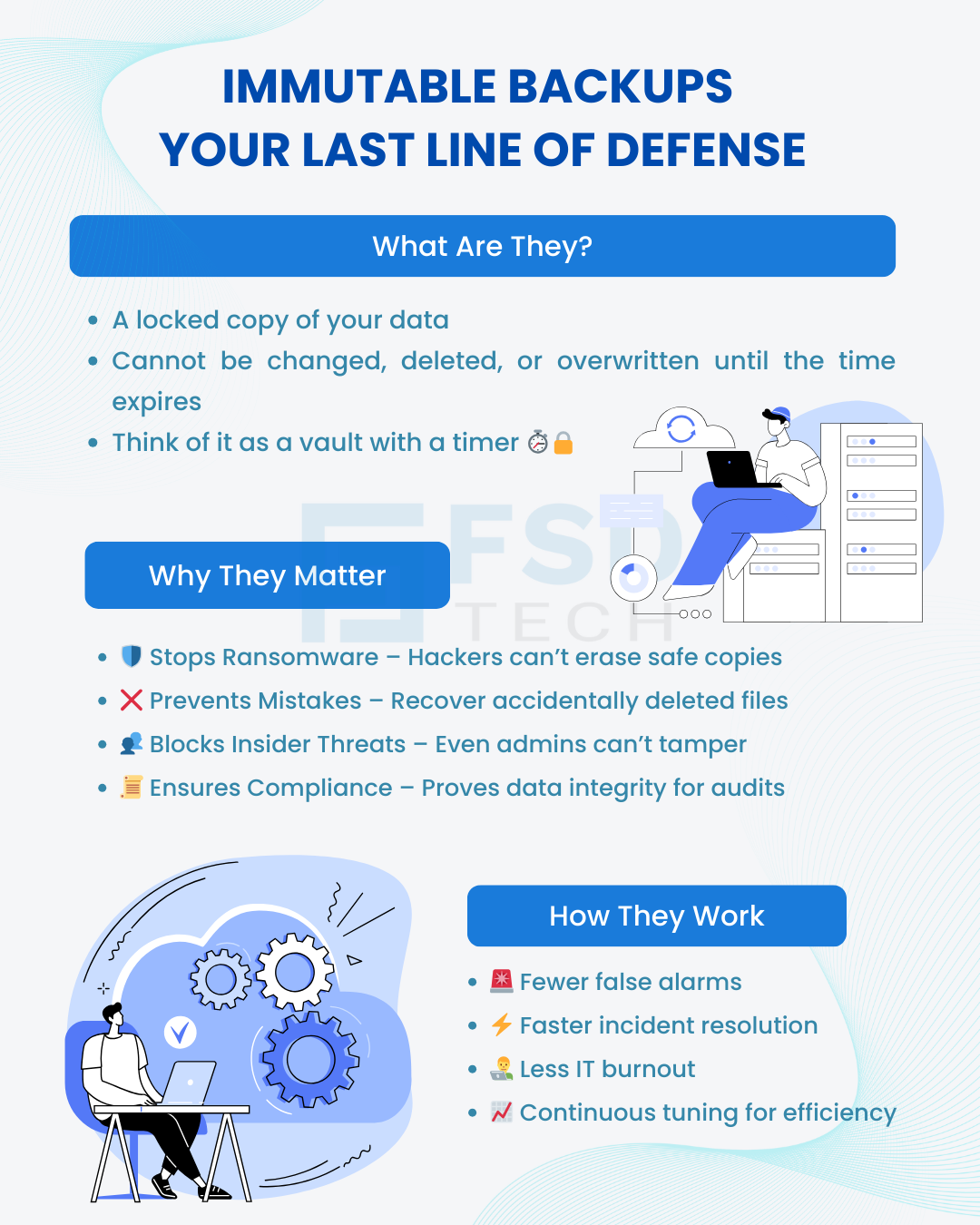
Immutable backups are locked for a set period of time.
No one — not even the system administrator — can delete or change them during this time.
They are safe from ransomware, mistakes, and insider sabotage.
Air-gapped backups are kept physically or logically disconnected from your main systems most of the time.
Think of it like storing a copy of your data on a hard drive that you unplug and lock away when you’re not using it.
It means you regularly test your backups to confirm:
Absolutely. Cloud-based backup tools make it simple and affordable for small companies to have multiple secure copies without needing a large IT department.
It depends on how much data you can afford to lose.
If losing one day’s work would be a big problem, back up daily.
If even losing an hour’s work would hurt your business, back up every hour or every few minutes.
Yes, if it’s hosted by a secure provider and has its own login credentials.
However, to make it truly safe, you should use immutability or air-gapping to prevent hackers from accessing and deleting it.
Vembu automates the 3-2-1-1-0 approach by:
Ask yourself:
If the answer to any of these is “no,” it’s time to improve your backup strategy.
Make a list of all the important data your business can’t afford to lose.
Then, work with a trusted provider like Vembu to:

Nasmal is a Solution Architect & Business Analyst focused on AI, Data, Automation, BCP, and Process Optimization. He helps businesses evolve from reactive to proactive, data-driven, and resilient operations. With hands-on expertise, he simplifies complex tech into clear, easy-to-understand blogs.
Share it with friends!
share your thoughts