.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Have you ever wondered who is actually sitting on the other side of a data breach? A threat actor is the person, group, or entity that acts with the intent to cause harm in the digital space. Whether they want to steal your credit card info or disrupt a government’s power grid, these individuals drive the world of cybercrime.
To be honest, the word "hacker" doesn't quite cover it anymore. In my experience, calling every attacker a hacker is like calling every athlete a professional soccer player. It’s a broad term that misses the nuance of their skills and goals. Are they doing it for money, for a political cause, or just for a "laugh"? Knowing who your enemy is helps you build a better defense.
Let’s look at why these groups exist and how they operate.
A threat actor (TA) can be anyone from a bored teenager in a basement to a highly trained military unit. Essentially, they are the "who" in the "who, what, where, and why" of a cyber incident. They look for weaknesses in your software, your hardware, or even your employees.
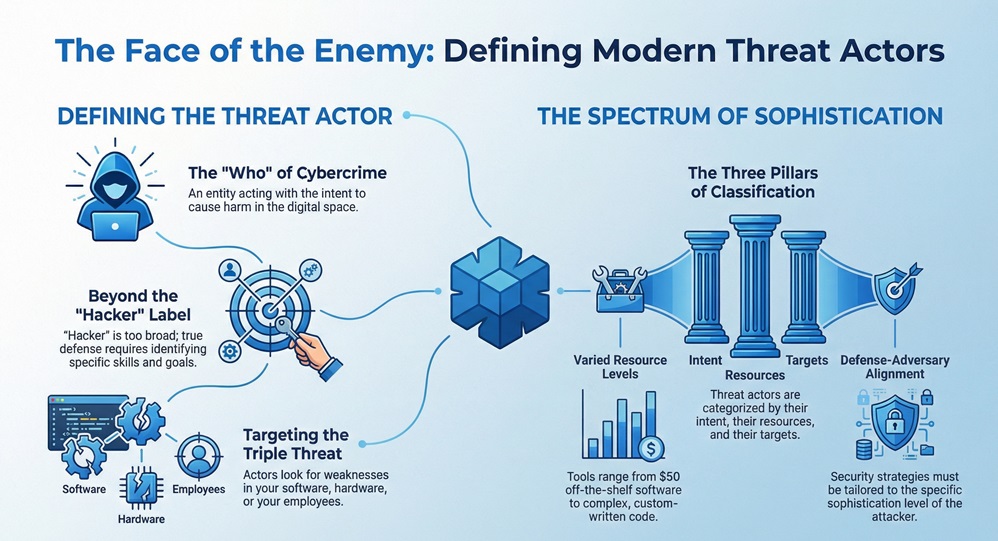
Here is the thing: not all attackers are equal. Some use "off-the-shelf" tools they bought for $50 on the dark web. Others write their own complex code that can bypass the world’s best firewalls. According to research from organizations like the CCDCOE, we can categorize these entities based on their intent, their resources, and their targets.
Why does this matter to you? Because your defense strategy depends on who is coming for you. You wouldn't use a screen door to stop a tank, right? Similarly, simple antivirus software might stop a script kiddie, but it won’t stop a nation-state.
When we talk about the "threat environment," we usually see a few recurring characters. Each has a different "MO" (Modus Operandi) and a different level of danger.
1. Cybercriminals (The Profit Seekers)
These are the most common threat actor types you will encounter. Their primary goal is money. They use ransomware, phishing, and identity theft to drain bank accounts or extort businesses. We have all seen the headlines about companies paying millions to get their data back. That is the work of organized cybercrime syndicates.
2. Nation-State Actors (The Digital Spies)
These groups work for a government. Their goals are usually espionage, political disruption, or economic theft. They are often called Advanced Persistent Threats (APTs). They have unlimited time and massive budgets.
3. Insider Threats (The Enemy Within)
This is a tough one to talk about. An insider is someone who already has access to your system—like an employee or a contractor. Sometimes they are malicious (disgruntled workers), but often they are just negligent. Did a staff member leave a laptop in a taxi? That is an unintentional insider threat.
4. Hacktivists (The Digital Protesters)
These actors attack for a cause. They might target a company they think is unethical or a government they disagree with. They often use DDoS attacks to take down websites and make a public statement.
Also Read: Perimeter Security: How to Protect Your Property Effectively
In my view, people often think they are "too small" to be a target. This is a dangerous mistake. Many threat actor groups use automated bots to scan the entire internet for any open door. They don't care who you are; they just care that you are vulnerable.
| Actor Type | Primary Goal | Skill Level |
|---|---|---|
| Cybercriminal | Financial Gain | Low to High |
| Nation-State | Espionage/Politics | Very High |
| Hacktivist | Social Change | Medium |
| Insider | Revenge/Money | Low to Medium |
How do they get in? Usually, it starts with the human element. Phishing is still the #1 way attackers gain a foothold. They send an email that looks like it's from your boss or your bank. Once you click, they are in.
A threat actor doesn't just click a button and win. It is a process. We often call this the "Cyber Kill Chain."
It sounds scary, doesn't it? But once you understand the steps, you can start breaking the chain.
Also Read: What is a Secure Web Gateway and How Does It Protect You?
We mentioned Advanced Persistent Threats (APTs) earlier. An APT is a long-term campaign where a threat actor stays inside a network for months or even years. They don't want to break things; they want to listen.
Imagine a guest staying in your guest room for a year without you knowing. They watch what you eat, hear your secrets, and know where you keep your money. That is what an APT group does to a corporate network. They are patient, and they are very hard to catch.
So, what can we do? We have all been there—feeling overwhelmed by the sheer number of risks. But protection doesn't have to be a nightmare.
To be honest, no defense is 100% perfect. The goal is to make it so difficult and expensive for the threat actor that they decide to move on to an easier target.
Understanding the threat actor is the first step in building a resilient business. While the digital world can feel like a "Wild West," we have better tools than ever to stay safe. At our core, we believe that security is about people protecting people. We're committed to helping you understand these risks so you can focus on what you do best. Your data is your legacy—let's keep it that way.

A hacker is a broad term for anyone who uses technical skills to bypass systems. A threat actor specifically refers to someone acting with malicious intent in a security context.
No. Insider threats involve people who already have legitimate access to your systems, such as employees or partners.
APTs are hard to find. Signs include unusual data transfers at odd hours or unknown files appearing on your servers.
Technically, no. The "actor" is the human or group behind the software. The software itself (like a virus) is just the tool they use.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts