.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

In 2026, the way we protect our digital assets has shifted from building walls to verifying every single movement. The Single Enterprise Perimeter Paradigm refers to the traditional "castle and moat" strategy where we focused all our energy on securing the network edge. We've all been there: you log into the office network, and suddenly, you have the keys to the kingdom. But as our work moves to the cloud and our teams go remote, that old-school wall is crumbling.
Here’s the thing—the world doesn't look like a single office anymore. We’re dealing with hybrid clouds, AI agents, and a workforce spread across the globe. To be honest, relying on one big perimeter in this day and age is a bit like putting a high-tech lock on your front door but leaving all the windows wide open.
This security model assumes that everything inside your company network is "safe" and everything outside is "bad." It uses tools like firewalls and VPNs to create a boundary. If you are inside the perimeter, the system trusts you.
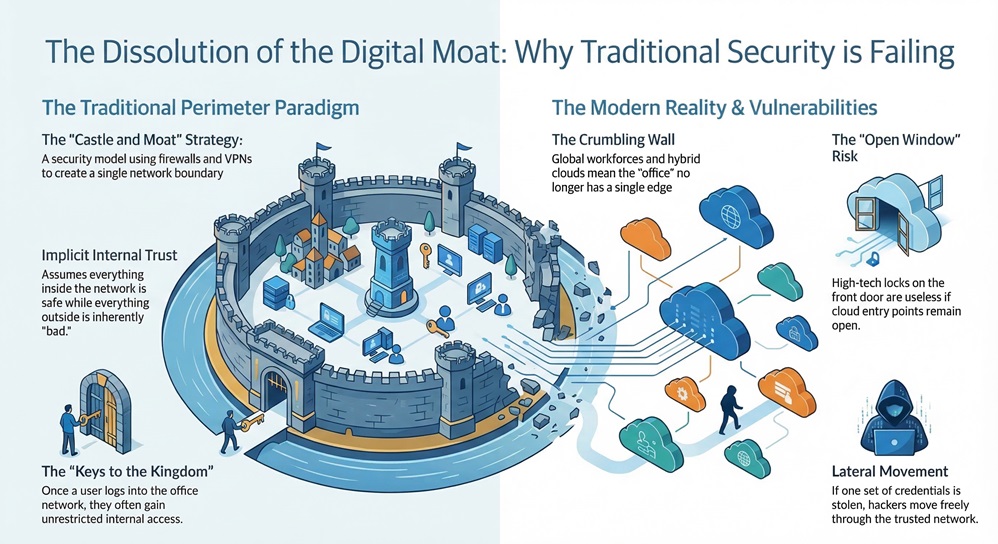
But wait, why is this a problem now? In my experience, the moment a hacker steals just one set of credentials, they can move through your entire system. This is called lateral movement. Since the paradigm assumes internal trust, there are very few checks once someone gets past the front gate.
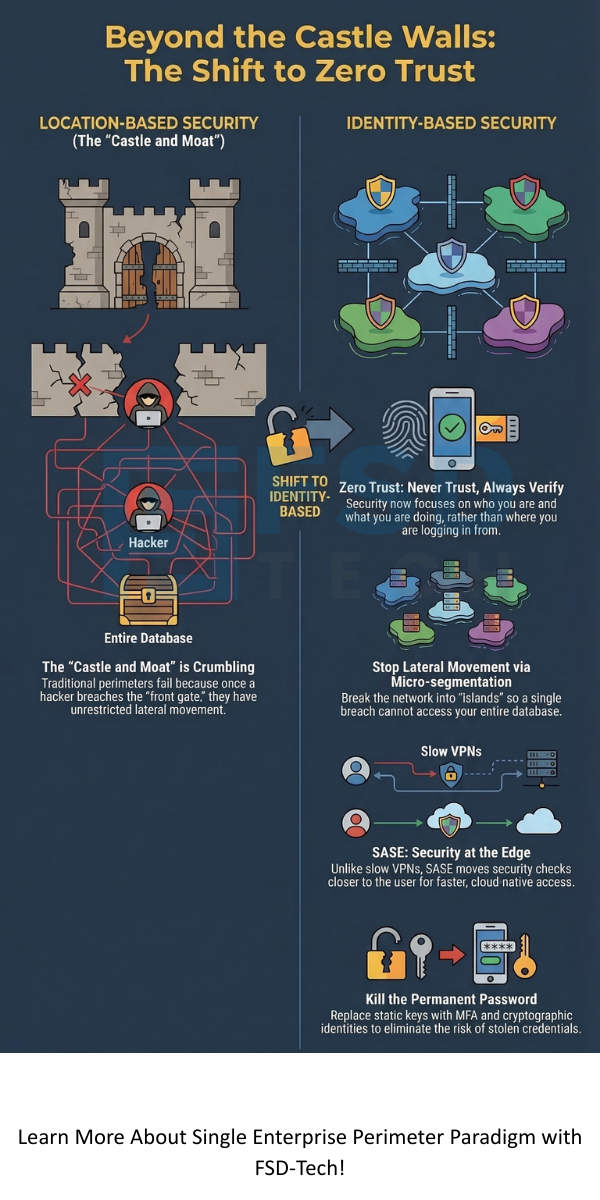
The Single Enterprise Perimeter Paradigm is slowly being replaced by Zero Trust Architecture (ZTA). While the old way focused on where you were connecting from, the new way focuses on who you are and what you are doing.
Picture this: in the old model, if a pirate boards your ship, they take the whole boat. In the new model, every room on the ship has its own biometric lock. One leak won't sink the whole vessel.
Also Read: Advanced Posture in Cato Client: Continuous Compliance Without User Friction
When we talk about moving away from a Single Enterprise Perimeter Paradigm, two names always come up: ZT and SASE.
| Feature | Single Perimeter Paradigm | Zero Trust (ZT) | SASE (Secure Access Service Edge) |
|---|---|---|---|
| Trust Model | Implicit (Trust if inside) | None (Never trust, always verify) | Identity-centric & Context-aware |
| Main Tools | Firewalls, VPNs | MFA, Micro-segmentation | SD-WAN, CASB, ZTNA |
| Location | On-premise / Data Center | Decoupled from location | Cloud-native / At the edge |
| Primary Goal | Keep outsiders out | Stop lateral movement | Secure access for the "everywhere" enterprise |
Have you ever wondered why your VPN feels so slow? That’s because the old paradigm often "backhauls" your traffic to a central data center before letting you go to the internet. It’s a massive bottleneck. Modern solutions like SASE fix this by moving the security check to the "edge"—closer to you.
Moving away from the Single Enterprise Perimeter Paradigm isn't a "flip the switch" situation. It’s a journey. In our view, it starts with identity.
1. Kill the Permanent Password
Stop relying on static keys. Use Multi-Factor Authentication (MFA) as your baseline. In 2026, we're even seeing a shift toward "passwordless" cryptographic identities. It's much harder for a hacker to spoof a hardware key than to guess "Password123."
2. Implement Micro-segmentation
Don't let your guest Wi-Fi talk to your financial server. By creating small, isolated zones, you reduce the "blast radius" of any potential breach. If a developer's laptop gets hit with malware, the malware shouldn't be able to "see" the HR database.
3. Focus on "Protect Surfaces"
The old paradigm tried to defend the "Attack Surface," which is huge and always changing. Instead, identify your "Crown Jewels"—your most sensitive data and apps. Build your strongest defenses around them first.
Also Read: Handling Unsupported or Legacy Clients in Cato Device Security Policies
At the end of the day, the Single Enterprise Perimeter Paradigm belonged to a simpler time. We've moved past the era of "set it and forget it" security. Today, your defense needs to be as dynamic as your business. We believe in building resilience that empowers your team to work from anywhere without fear.
Our goal is to help you bridge the gap between legacy systems and the secure, cloud-first future. We don't just protect data; we protect the people and the innovation that drive your company forward.
Not exactly. You still need firewalls, but they are no longer your only line of defense. Think of it as adding internal security guards to a building that already has a front door lock.
Lateral movement. If a hacker gets past the perimeter, they can roam free. Most major data breaches happen because the internal network was too "flat" and trusting.
Definitely not. While a VPN creates a tunnel to a network, SASE provides a whole suite of security (like ZTNA and Web Gateways) directly in the cloud. It’s faster and much more secure

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts