.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
A blue team refers to the internal security professionals who defend an organization against real-world cyber threats and simulated attacks. Think of them as the silent guardians of the digital realm. While hackers and "red teams" get the Hollywood glory for breaking into systems, the blue team does the heavy lifting to keep the doors locked.
Are you curious about how companies actually stay safe when thousands of attacks happen every minute? To be honest, it’s not just about installing an antivirus and hoping for the best. It's a structured, constant battle.
In this guide, we'll look at how these defensive experts operate. We’ll explore their daily tasks, the tools they use, and why they are the backbone of any modern business.
The blue team is a group of specialized individuals dedicated to protecting an organization's digital assets. Their primary job is to maintain the security posture of the network. They don’t just wait for something to break. Instead, they proactively look for holes, monitor traffic, and respond to incidents the moment they occur.
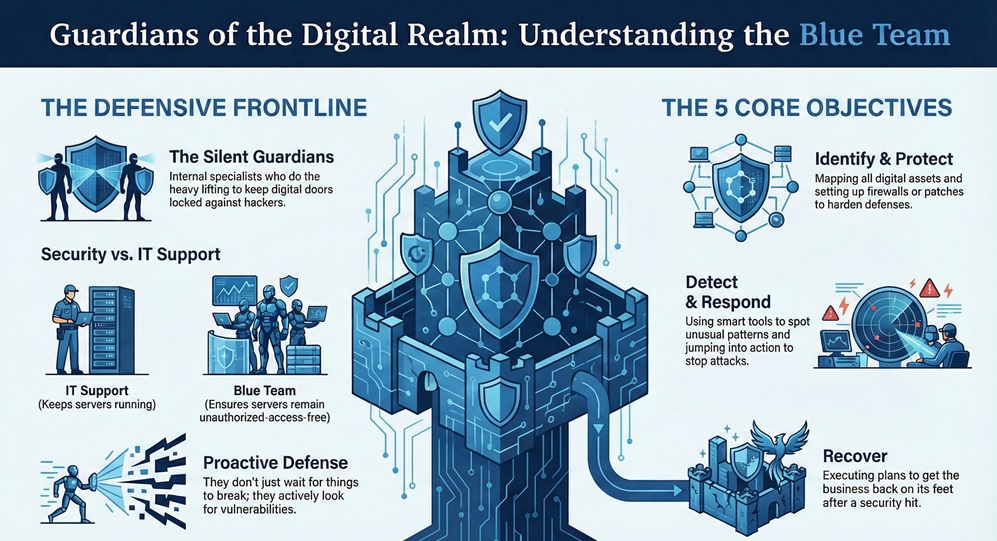
In my experience, many people confuse them with general IT support. That’s a mistake. While IT keeps the servers running, the defensive security team ensures those servers aren't being used by a stranger in another country.
You might wonder, who actually sits on these teams? It isn't just one person doing everything. A mature security unit has various roles that work together like a well-oiled machine.
1. Security Analysts
These are the first responders. They spend their day looking at screens filled with alerts. Their goal? To decide if a "login attempt from Brazil" is a traveling employee or a thief.
2. Incident Responders
When a breach is confirmed, these folks take over. They follow a strict "playbook" to isolate infected computers and kick the attacker out. Have you ever seen a team move with military precision during a crisis? That's them.
3. Threat Hunters
This is a more advanced role. Instead of waiting for an alert, they go looking for trouble. They assume an attacker is already inside and search for tiny clues that automated tools might miss.
4. Security Engineers
They build the "digital citadel." These engineers configure the tools, manage the log pipelines, and ensure that the defense infrastructure is actually working.
Also Read: Avoiding Compliance Penalties with Cato SASE: Meeting Regulatory Standards Effortlessly
We can’t talk about defense without mentioning offense. In the world of security exercises, the red team acts as the "bad guys." They are ethical hackers hired to find a way in.
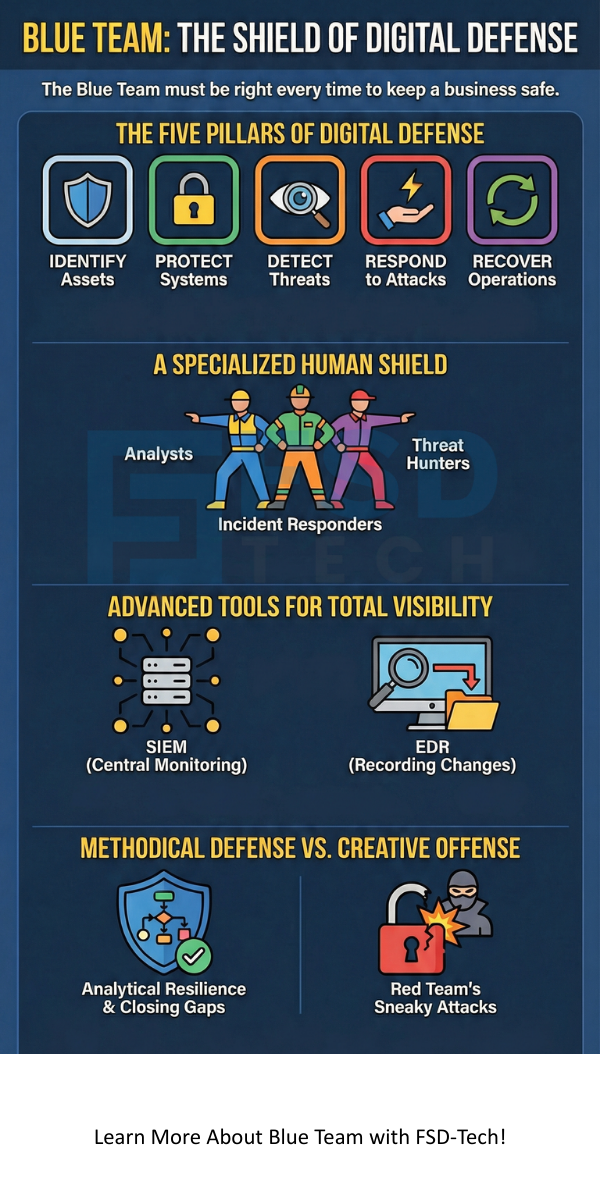
The blue team stands on the opposite side. While the red team tries to be sneaky, the defenders try to be vigilant. Roughly 70% of a company’s security maturity comes from these two teams playing against each other. We call this a "purple team" exercise when they share notes to get better.
| Feature | Red Team | Blue Team |
|---|---|---|
| Focus | Offense (Attacking) | Defense (Protecting) |
| Goal | Exploit vulnerabilities | Detect and remediate |
| Mindset | Creative, sneaky, destructive | Methodical, analytical, resilient |
| Outcome | Finds the gaps | Closes the gaps |
To stay ahead of modern threats, a blue team uses a sophisticated stack of software. We've moved past simple firewalls. Today, it’s all about visibility and automation.
SIEM (Security Information and Event Management)
Tools like Splunk or Microsoft Sentinel act as a central brain. They collect logs from everywhere—your email, your cloud, your wifi—and look for connections. If a user logs in from New York and two minutes later from London, the SIEM screams for help.
EDR (Endpoint Detection and Response)
Think of EDR as a black box flight recorder for every computer in the office. It records every process and file change. If a virus starts encrypting files, the EDR can often kill the process automatically.
Open-Source Favorites
Many teams use powerful open-source tools to save on costs while staying sharp:
Also Read: Unified Device Visibility: Enhancements to Cato’s Device Inventory
Picture this: It’s 2:00 PM on a Tuesday. A Security Analyst gets a notification. Someone in accounting just clicked a suspicious link in an email. This is where the blue team shines.
First, they triage the alert. Is it a false alarm? To be honest, many are. But if it’s real, they move to containment. They might disable the user’s account and disconnect their laptop from the network.
Next comes the "eradication" phase. They find the malicious file and delete it. Finally, they perform a post-mortem. We've all been there—sitting in a meeting asking, "How did this happen?" The team uses these lessons to update their firewalls so the same trick won't work twice.
Does this sound like something you'd enjoy? The demand for defensive pros is higher than ever. Here is a simple path to get started:
The blue team is much more than a group of IT experts; they are the strategic heart of a company's survival. By combining advanced tools with a methodical mindset, they ensure that your data stays private and your systems stay online.
At FSD-Tech, we believe that security is a human right for every business. We focus on building resilient defenses and empowering our clients to face the future without fear. Our values center on transparency and relentless protection, because your trust is our most valuable asset.
In my view, it’s attention to detail. You are looking for a needle in a haystack of data. Missing one small log entry could mean missing a full-scale breach.
That’s a tough one! To be honest, they are just different. A red team only has to be right once to get in. A blue team has to be right every single time to stay safe.
You don't need to be a software developer. However, knowing a bit of Python or PowerShell helps you automate boring tasks. It makes you much faster at responding to threats.
A SOC is a Security Operations Center. It is the physical or virtual room where the blue team works. It’s the command center for all things security.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts