.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

Antibot technology acts as your first line of defense against the silent, automated scripts that crawl the web to steal data or disrupt services. Have you ever wondered why your website traffic spikes suddenly, but your sales stay the same? Or perhaps you've noticed strange login attempts from countries where you don't even have customers. These are often the footprints of "bad bots."
In my experience working with network security, I've seen how a single undetected bot can drain bandwidth and scrape proprietary pricing in seconds. It’s a game of cat and mouse. While some bots help search engines find you, others work for hackers. An antibot solution helps you tell the difference. It isn't just about blocking traffic; it's about protecting your brand's integrity.
An antibot system uses a multi-layered approach to catch malicious scripts. Think of it like a smart security guard at a private club. The guard doesn't just look at a guest's ID; they watch how the guest walks, talks, and interacts with others.
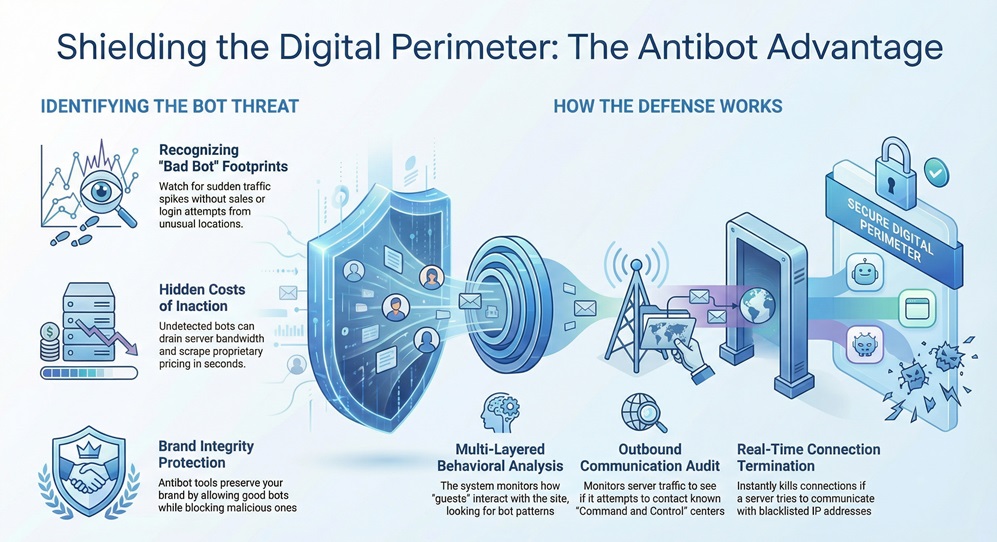
According to technical documents from leaders like Check Point, these tools look for specific "bot patterns." They monitor outbound communication from your servers to see if they're trying to talk to known "Command and Control" (C&C) centers. If your server suddenly tries to send a packet of data to a blacklisted IP address in the middle of the night, the antibot software steps in to kill the connection.
Wait, why do we need to detect infections after they happen? To be honest, no firewall is 100% foolproof. Sometimes a user accidentally clicks a phishing link, and a bot gets inside your perimeter. This is where antibot tools shine. They provide "post-infection" visibility.
By analyzing the DNA of the traffic, the software identifies infected hosts within your network. It looks for "phone home" attempts. Once it finds an infected device, it blocks the outgoing data. This prevents the bot from "reporting back" to its master, effectively neutralizing the threat even if the malware is already on the machine.
You might think your standard firewall is enough. However, bots have become incredibly sophisticated. Modern automated threats use "headless browsers" that mimic human behavior perfectly. They can move the mouse, click buttons, and even solve simple puzzles.
Standard security often looks at "what" the traffic is. An antibot solution looks at "how" the traffic behaves. It uses a massive database of bot fingerprints. These fingerprints are updated constantly. If a new bot strain appears in Europe, your system in New York knows about it within minutes. This global intelligence is the "secret sauce" of modern cybersecurity.
Also Read: Network Firewalls vs. Next-Generation Firewalls: Which One Wins?
As businesses move to the cloud, the "virtual" landscape changes the rules. When you run servers in a virtual environment, you need an antibot solution that can scale. Check Point’s research highlights that virtual security must be as agile as the virtual machines themselves.
In these setups, the antibot software usually sits at the virtual gateway. It inspects traffic between virtual machines (East-West traffic) and traffic leaving the cloud (North-South traffic). This prevents a bot from jumping from one virtual server to another. If one "pod" gets hit, the rest of your cloud stays safe.
How do we actually spot a bot in a sea of millions of users? It's not as easy as it sounds. We use several layers of analysis to make a decision.
1. Reputation-Based Filtering
This is the simplest form. The system maintains a list of known "bad" IP addresses. If a request comes from a server known for hosting malware, the antibot blocks it immediately. It’s effective, but it only catches the "dumb" bots.
2. Signature Matching
Every bot has a "signature" or a specific bit of code that gives it away. Security researchers analyze malware samples and create these signatures. When the traffic matches a signature in the database, the alarm goes off.
3. Behavioral Analysis
This is my favorite part. Behavioral analysis doesn't care what the bot looks like; it cares what it does. For example, a human takes about 1-2 seconds to read a headline before clicking. A bot clicks the next link in 0.001 seconds. When the antibot sees this "superhuman" speed, it knows it's dealing with a script.
Also Read: What is Unified Endpoint Management and Why Does Your Team Need It?
Here is the thing: many small business owners fear that high-level security will slow down their website. In reality, modern antibot tools are designed to be "invisible." They use low-latency inspection. This means they check the traffic so fast that your real customers never notice a delay.
In my view, the risk of not having protection is much higher. Think about the cost of a data breach. If a bot steals your customer database, the legal fees and loss of trust could ruin you. We've all been there—trying to save a few dollars on tools only to pay ten times more later to fix a mess.
A good tool should tell you exactly what it's doing. You shouldn't need a PhD in computer science to read the reports. Most platforms provide a dashboard that shows:
This visibility allows your IT team to focus on the real problems instead of chasing shadows. Instead of wondering "why is the server slow?", you can see that an antibot just stopped a massive scraping attempt.
The digital world is full of automated noise. To keep your business running smoothly, you need a way to filter out the malicious scripts while letting the real people in. Antibot protection isn't just a "nice-to-have" anymore; it's a fundamental part of staying online.

At FSD-Tech, we believe that security should empower your business, not slow it down. We focus on providing solutions that are easy to use and incredibly effective. Don't wait for a bot to crash your site or steal your data. Take a proactive step toward a safer digital future today.
No. Sophisticated tools have a "whitelist" for good bots like Googlebot or Bingbot. This ensures your SEO rankings aren't affected while bad actors are kept out.
Not exactly. An Antivirus looks for files on your computer. An antibot looks at the communication patterns and traffic flow to identify bot-like behavior.
Yes. Bots don't care about the size of your business. They look for vulnerabilities. In fact, smaller sites are often easier targets because they have weaker security.
Most modern solutions can decrypt and inspect traffic (with proper certificates) to ensure no bots are hiding inside encrypted packets.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts