.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Perimeter-less security refers to a modern IT strategy that moves protection away from a single corporate office and places it directly where your data and users live. To be honest, the old way of "locking the front door" of your office just doesn't work anymore.
In my experience, many IT teams still try to force all their traffic through one central data center. Why do we do this? Historically, we thought that keeping everything in one place gave us control. But here is the thing: your team is now working from home, in coffee shops, and on the road. Your apps have moved to the cloud, too.
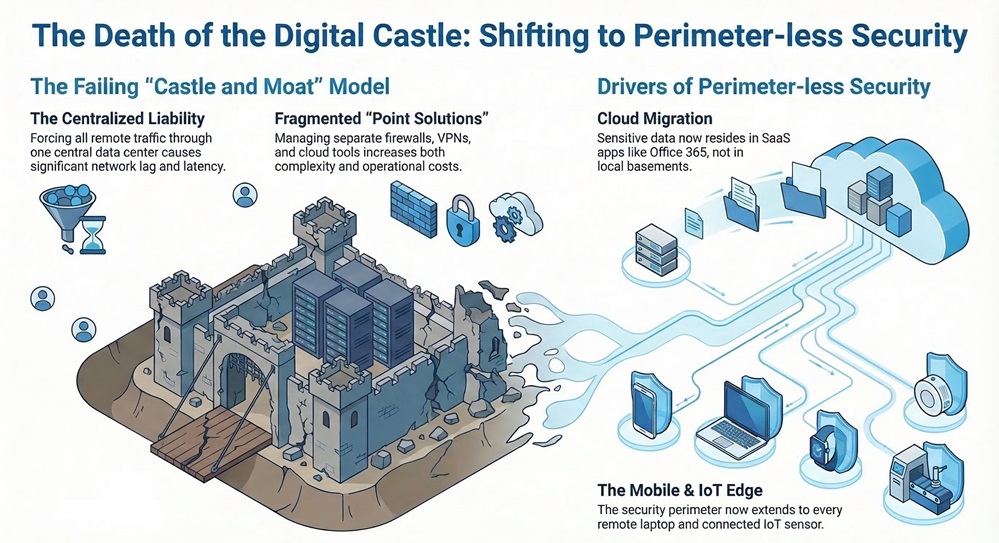
This shift has turned the traditional "moat and castle" model into a liability. Have you ever wondered why your network feels slow when you're using a VPN? It is usually because your data is traveling hundreds of miles out of its way just to be "checked" at the office before going to the internet.
The traditional network perimeter was a physical boundary drawn around a corporate data center. It worked well when every employee sat at a desk in the same building. But the world changed.
As these networks expanded, IT teams started piling up "point solutions" to fix new problems. You might have a firewall for the office, a separate VPN for remote users, and another tool for cloud security. This makes everything too complicated and expensive. We've all been there—trying to manage ten different dashboards just to see if the network is safe.
Also Read: Autonomous Platform Life Cycle Management: How SASE Is Redefining Enterprise Network Operations
So, how do you secure a world without boundaries? You choose the SASE way. Secure Access Service Edge, or SASE, is a term coined by Gartner in 2019. It isn't just a single product; it's a way of thinking that combines networking and security into one global cloud service.
Instead of a physical box in your office, the "perimeter" becomes a software layer that follows the user. Whether you are in New York or London, you connect to a nearby Point of Presence (PoP) in the cloud. This PoP checks your identity and makes sure you're safe before letting you access anything.
To make this work, a true SASE platform needs four main traits:
Also Read: SASE for Industry 4.0: Securing the Future of Connected Manufacturing
I've seen how this helps different sectors. Take retail, for example. Many stores used to rely on expensive MPLS links that were slow and hard to manage. With a perimeter-less approach, they can use simple internet connections to stay secure and save money.
In manufacturing, Industry 4.0 is bringing "smart factories" to life. But these factories are huge targets for hackers. By using SASE, manufacturers can protect their vulnerable IoT devices without slowing down their production lines.
Transitioning to a perimeter-less model doesn't happen overnight. Many companies start by replacing their old VPNs with Zero Trust Network Access (ZTNA). Others might start by migrating from MPLS to SD-WAN to save on costs.
The goal is to stop agonizing over complex hardware and start focusing on what matters: your business. SASE allows you to deliver a great user experience without compromising on safety.
At Cato Networks, we believe that security should be simple, global, and ready for whatever comes next. We are dedicated to helping you shed the weight of legacy systems so you can focus on growth. Our focus is always on your success, providing a platform that is as agile as your business needs to be.

A VPN usually connects a user to a specific office network, which can be slow and less secure. SASE connects users to a global cloud that applies security and optimization at the same time.
Actually, it often saves money. By consolidating many point products into one service, you reduce the costs of procurement, integration, and maintenance.
Yes. Because SASE is cloud-native and delivered as a service, it allows organizations of all sizes to get enterprise-grade security without a huge IT staff.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts