.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
The Fourth Industrial Revolution isn't just a buzzword anymore—it's your new daily reality. If you walk onto a factory floor today, you'll see a world that would have looked like science fiction a decade ago. Sensors track every vibration of a CNC machine, robots coordinate with autonomous carts, and cloud-based AI predicts a part failure before it even happens.
But here’s the thing: while your production line has leaped into the future, your network might still be stuck in the past.
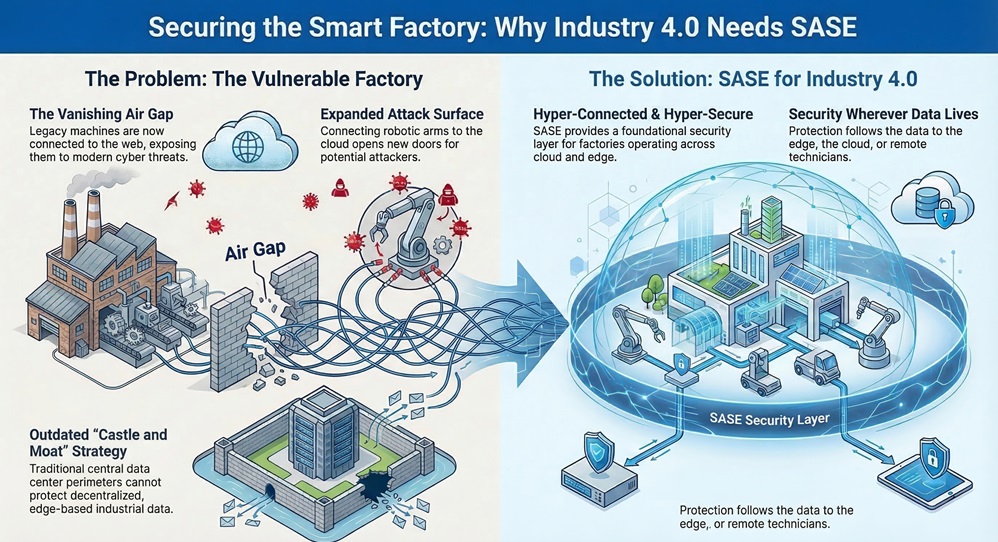
For years, we’ve relied on a "castle and moat" strategy. We put all our sensitive data in a central datacenter and built a massive wall around it. But Industry 4.0 has blown those walls down. Today, your data is everywhere—on the edge, in the cloud, and in the pocket of a technician working from home.
This is where SASE for Industry 4.0 comes in. It’s not just a technical upgrade; it's the foundation for a factory that is both hyper-connected and hyper-secure.
In my experience, the move toward "Smart Factories" is a classic double-edged sword. On one side, you have incredible efficiency. On the other, you have a massive increase in your "attack surface."
Historically, Manufacturing Technology (OT) was air-gapped. It didn't touch the internet, so it was relatively safe from hackers. Fast-forward to today, and that air gap is gone. Your IoT devices need to talk to cloud applications to give you those sweet predictive insights.
The problem? Most of these machines were never built with modern cyber threats in mind. They are "legacy" in a world of "advanced" threats. When you connect a 15-year-old robotic arm to the web, you aren't just gaining data—you're opening a door for attackers.
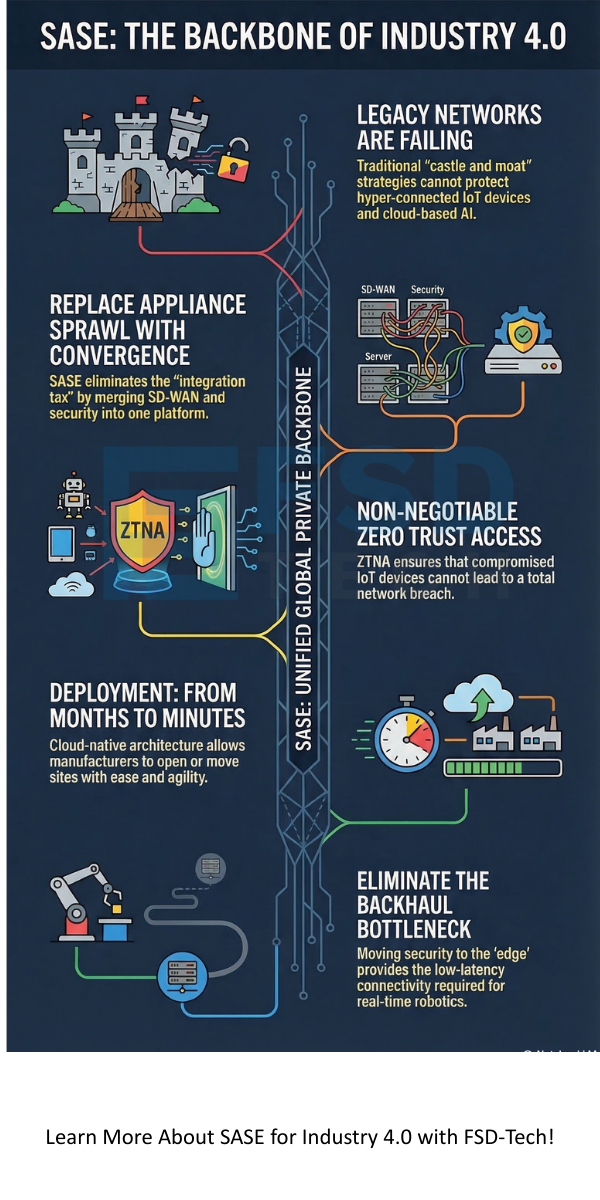
If you’re still using traditional MPLS or a bundle of point solutions, you’ve likely felt the "integration tax." We've all been there—trying to get a firewall from one vendor to play nice with an SD-WAN tool from another, all while your IT team spends 80% of their time just "keeping the lights on."
1. The Complexity Trap
As your factory grows, you keep adding boxes. A VPN for remote contractors, a CASB for cloud apps, and a stack of firewalls for every branch. This "appliance sprawl" makes your network slow, expensive, and incredibly hard to manage.
2. The Backhaul Bottleneck
Traditional networks often "backhaul" all traffic to a central hub for security scrubbing. Imagine a sensor in a Dubai factory trying to send data to a cloud app, but it first has to travel to a datacenter in London just to be checked by a firewall. This latency kills the "real-time" promise of Industry 4.0.
3. The Security Blind Spot
Point solutions create silos. Your network team sees one thing, and your security team sees another. This lack of a "single pane of glass" means threats can hide in the gaps between your tools.
Also Read: IT/OT Convergence in SASE: How to Secure the Smart Factory
Secure Access Service Edge, or SASE (pronounced "sassy"), changes the game by converging networking and security into a single, cloud-native service. Instead of a pile of hardware, you get a global private backbone that handles everything.
To be honest, the best way to understand SASE for Industry 4.0 is to see it in action. Take the example of a global manufacturer like the Flügger Group. They were struggling with the rigid nature of MPLS. Every time they wanted to open a new location or integrate a partner, it was a headache of hardware and configuration.
By migrating to a SASE architecture, they replaced their heavy MPLS links with simple "sockets" that connect to a global cloud. The result? They could open, move, or close sites with ease. Security was no longer a hurdle; it was a built-in feature.
Also Read: Auto-Adaptive Threat Prevention: How SASE Stops Modern Cyberattacks
You have two choices when scaling your smart factory.
The Hard Way: You "integrate with sweat and tears." You buy point solutions, hire expensive experts to stitch them together, and deal with constant troubleshooting. You're effectively building a Frankenstein's monster of a network.
The SASE Way: You adopt a unified platform. One policy, one console, and one global backbone. It’s like trading in a garage full of specialized tools for a single, high-powered Swiss Army knife that upgrades itself automatically.
While SASE is a horizontal technology, it hits differently depending on your industry:
Regardless of your field, the goal remains the same: simplify the network so you can accelerate the business.
The shift to Industry 4.0 is inevitable. You can't compete in a global market with manual processes and disconnected data. But as you build this new, digital future, don't leave your security behind.
In this section, we’ve seen that traditional networking just can't keep up with the speed and risk of a modern factory. SASE isn't just a "security product"—it's an architecture that empowers you to be bold. It gives you the confidence to connect more devices, move more data to the cloud, and empower more remote workers without losing sleep over the next big breach.
At FSD-Tech, we believe that networking should be simple, and security should be baked in. Thus, we can conclude that the SASE way is the only way to truly "future-proof" your enterprise perimeter.
Ready to see how SASE can transform your production line?
Not immediately. SASE is a journey. Most companies start with a specific "entry point"—like replacing a legacy VPN or securing a new cloud application—and gradually phase out old hardware as it reaches its end of life.
This is a common worry. SASE protects these devices at the network level. By using a "socket" or a secure tunnel, the SASE cloud wraps a security layer around that old machine, inspecting its traffic and blocking threats before they reach it.
In my view, you have to look at the Total Cost of Ownership (TCO). While the subscription might seem comparable, you save massively on hardware refreshes, vendor management, and the "time-cost" of your IT team. Most firms find SASE is significantly more cost-effective over a 3-year period.
Actually, SASE is great for this. Because it uses a global private backbone, it can optimize even "dirty" internet links, providing a much more stable experience than a standard VPN over the public web.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts