.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026

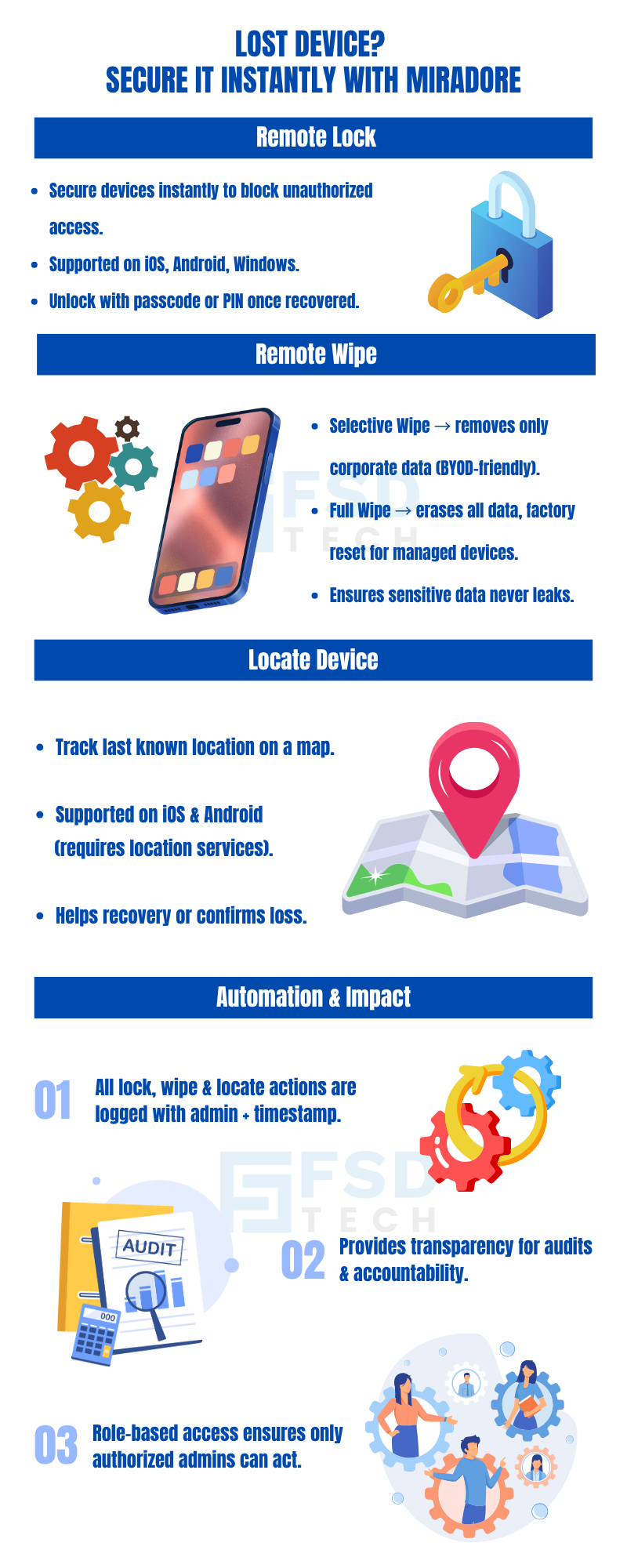
In today's mobile-first world, the risk of devices being lost or stolen is a significant concern for organizations. Such incidents can lead to unauthorized access to sensitive data, potential data breaches, and compliance issues. Therefore, it's imperative for IT administrators to have robust tools to manage and mitigate these risks.
Miradore provides a comprehensive suite of features to address these challenges. Through its platform, administrators can remotely lock, wipe, and locate devices, ensuring that even if a device is lost or stolen, organizational data remains secure.
The remote lock feature allows administrators to secure a device remotely, ensuring that unauthorized users cannot access its contents.
Miradore offers two types of wipe actions to ensure data security:
For supported devices, Miradore provides the ability to track the device's location:
Miradore ensures transparency and accountability by logging all remote actions:
Consider a scenario where an employee misplaces their company-issued Android tablet during a business trip:
This approach demonstrates how Miradore's features can be effectively utilized to manage lost or stolen devices while maintaining data security.
To further enhance your organization's device security posture:
Want to see how Miradore’s remote lock, wipe, and locate features work in real time? Schedule a Free session with our experts.
Yes. The lock command will execute automatically when the device comes online.
No. It only removes corporate apps, settings, and data while leaving personal files intact.
No. Full wipe is supported on fully managed Android and Windows devices.
Location tracking requires location services; without it, only the last known connection point may be available.
Yes. Every lock, wipe, or locate action is recorded with administrator details, device information, and timestamps.
No. A full wipe restores factory settings and removes all data. Recovery is not possible, so this should only be used for unrecoverable or retired devices.
Selective wipe ensures personal data remains untouched while corporate apps and profiles are removed, preserving employee privacy.
Yes. Role-based access control allows assigning permissions so only authorized administrators can execute remote commands.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
.webp&w=3840&q=75)
🕓 March 25, 2026

🕓 March 22, 2026

🕓 March 20, 2026
share your thoughts