.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
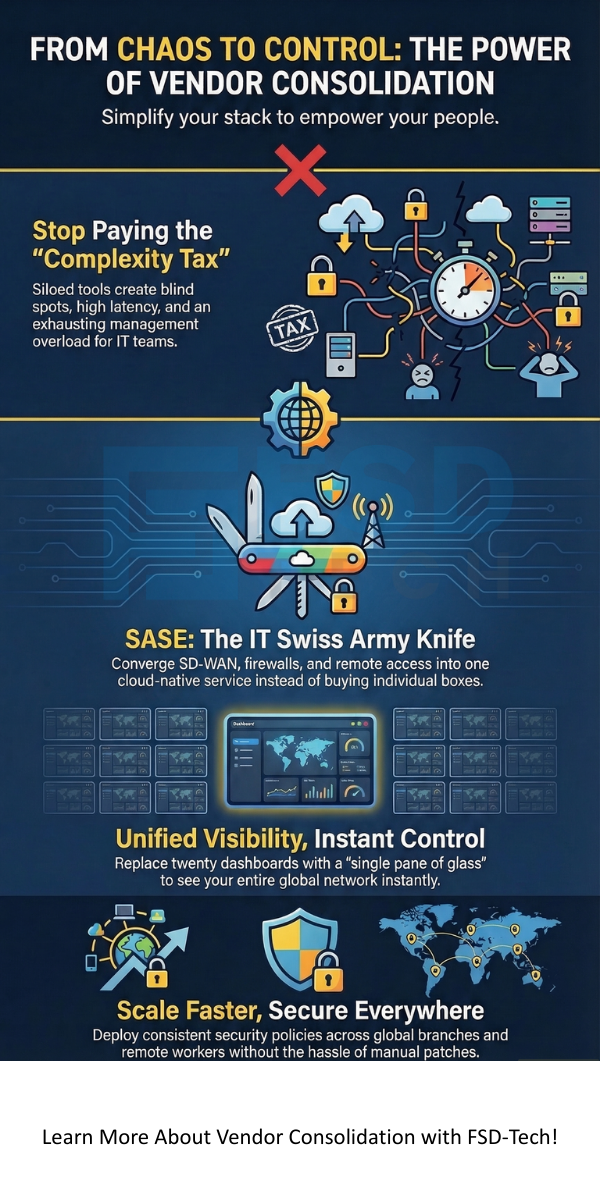
Vendor consolidation helps you reclaim control over your sprawling network and security stack without the "sweat and tears" of manual integration. Let’s be real for a second. We’ve all been there: staring at a "Frankenstein" architecture where five different firewalls, three VPNs, and a messy SD-WAN setup all fight for attention. It’s expensive, it’s slow, and it’s honestly exhausting. But what if you could trade that chaos for a single, unified platform?
In my experience, the push for more "best-of-breed" tools often backfires. You end up with a pile of point solutions that don't talk to each other. This forces your team to spend their days troubleshooting instead of innovating. Fast-forward to today, and the Secure Access Service Edge (SASE) model is changing the game by converging everything into one cloud-native service.
Are you tired of managing twenty different dashboards just to keep the lights on? Here is the thing: simplifying your vendor list isn't just about saving money; it's about regaining your sanity.
Start Your Consolidation Journey
Historically, IT teams solved every new problem by buying a new gadget. Need better branch security? Buy a Next-Generation Firewall (NGFW). Need remote access? Add a VPN. Before you know it, you’re paying a "complexity tax" that goes way beyond the invoice.
Also Read: Why Traditional Network Security Fails Against Modern Threats and How Cato SASE Fixes It
When we talk about vendor consolidation today, we're really talking about moving to a SASE architecture. Gartner defined SASE in 2019 as the convergence of networking and security into a single cloud service. Instead of buying five different boxes, you get one platform that handles it all.
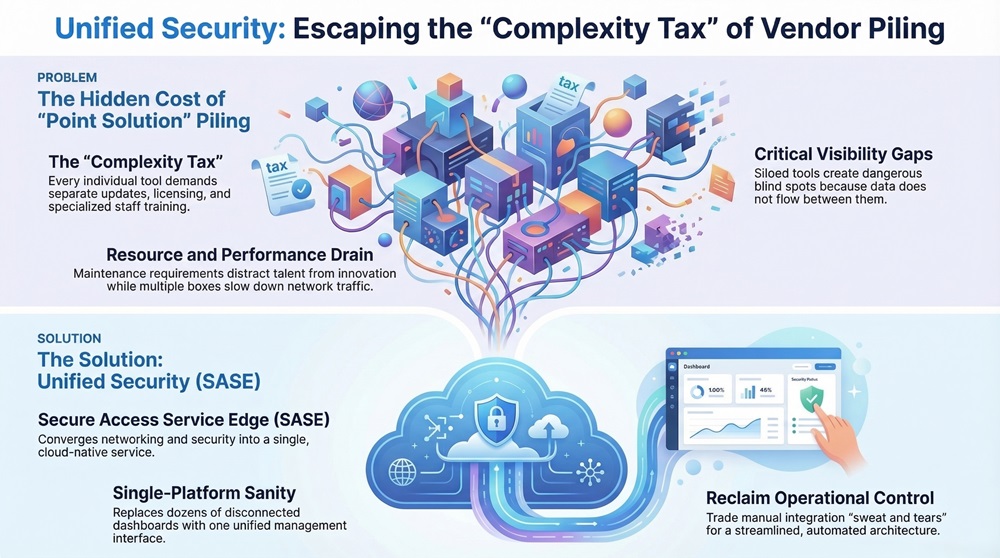
Picture this: your SD-WAN, Firewall as a Service (FWaaS), and Zero Trust Network Access (ZTNA) all living in one place. It’s like trading a heavy bag of individual tools for a high-tech Swiss Army knife. This unified approach makes your network more agile and much easier to protect.
In my view, industries with many locations feel the most pain from vendor sprawl. For example, a manufacturer with "smart factories" needs to secure thousands of IoT devices that weren't built with security in mind. Managing separate security tools at every factory is a nightmare.
By consolidating with a provider like Cato Networks, companies can connect every branch and cloud resource to a global private backbone. This ensures that security policies are the same everywhere—whether the user is in a factory in Vietnam or working from home in London.
Also Read: Bypassing the Cato Cloud Using Predefined Applications: Simplify Secure Egress for Key Traffic
You might wonder, "Don't I lose control if I put all my eggs in one basket?" To be honest, the opposite is usually true. A single-vendor SASE platform gives you better control because you have a "single pane of glass" for everything. You don't have to guess which tool is failing; you can see the whole picture instantly.
At the end of the day, vendor consolidation isn't just a trend; it's a survival tactic for the modern enterprise. We've seen how "piling up" point solutions creates a slow, expensive, and risky environment. By choosing a unified SASE path, you're not just simplifying your tech—you're empowering your people. At FSD-Tech, we're dedicated to making networking and security so simple that you can finally get back to what you do best. Let's build a future where your network works for you, not the other way around.
Not necessarily. Modern SASE platforms use "best-of-breed" engines that are updated automatically in the cloud. You get high-end security without the hassle of manual patches.
Most organizations use vendor consolidation to migrate away from expensive, rigid MPLS. You can switch to affordable broadband while maintaining "private backbone" performance through SASE.
Yes! A converged platform includes ZTNA, meaning remote users get the same security and optimization as people in the office.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts