.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
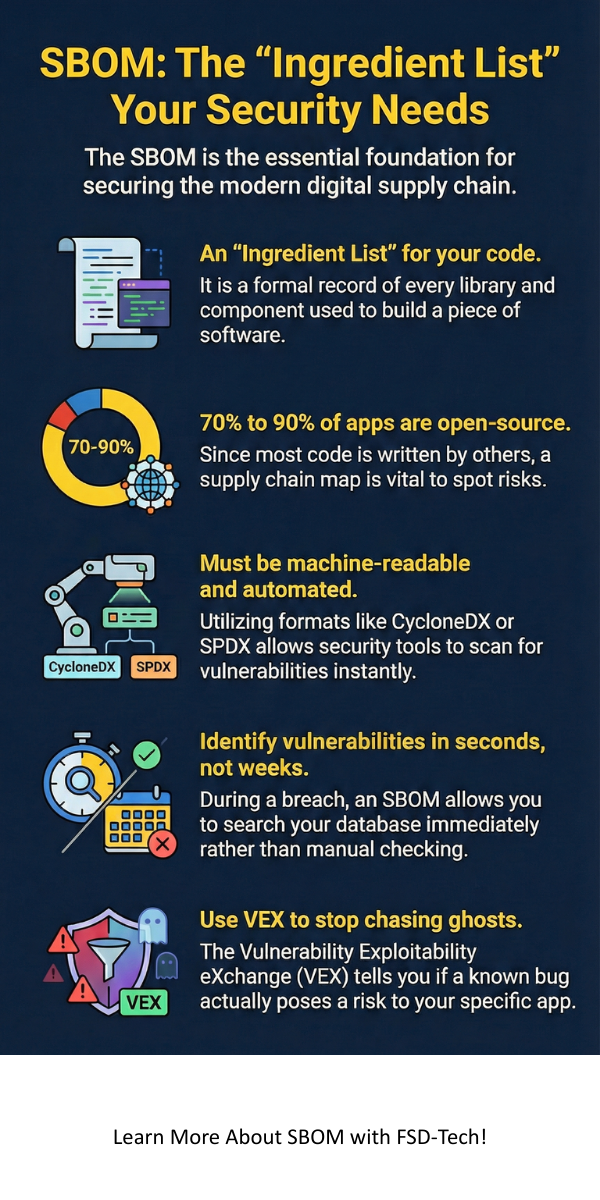
Have you ever looked at the back of a cereal box? You see a list of every ingredient, from corn to riboflavin. You know exactly what you're eating. Now, think about the software your company uses. Do you know every "ingredient" inside it? Most people don't. This is where a Software Bill of Materials comes into play.
In my experience, many teams treat software like a black box. They buy it, install it, and hope for the best. But here is the thing: modern software is like a giant LEGO set. Developers rarely write everything from scratch. Instead, they use open-source libraries and third-party code. If one of those small pieces has a security hole, your entire system is at risk.
An SBOM is basically that ingredient list for your code. It tells you what is inside, who made it, and what version it is. Without this list, finding a bug is like looking for a needle in a haystack. But with a Software Bill of Materials, you can spot risks before they become disasters. Are you ready to see what is actually hiding in your apps?
The term Software Bill of Materials refers to a formal, structured record that outlines the supply chain relationships of various components used in building software. Think of it as a nesting doll. One piece of software contains five libraries, and each of those libraries might contain three more. An SBOM tracks all of them.
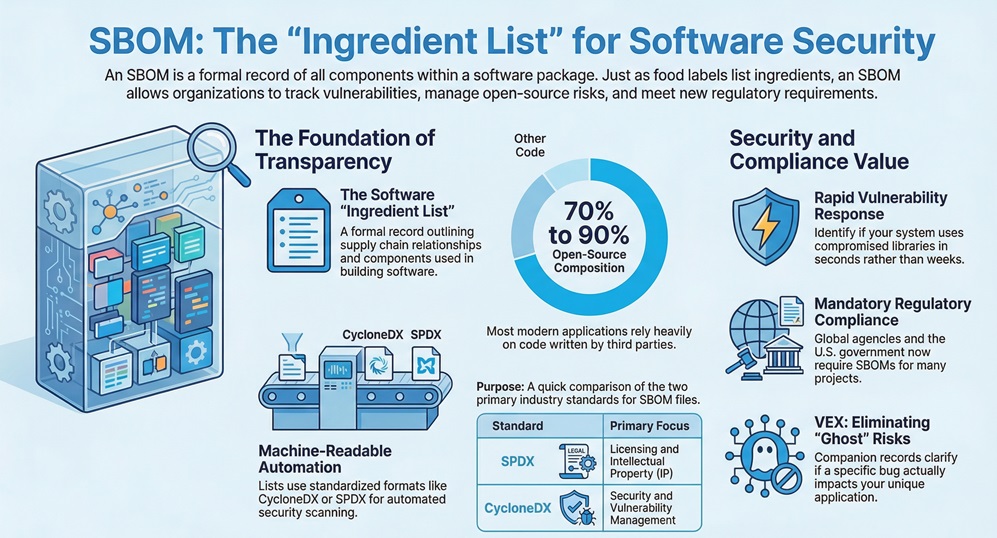
We call these lists "machine-readable." This means they aren't just for humans to read over coffee. AI bots and security tools read them too. This allows for automated scanning. If a new vulnerability drops tomorrow, your tools can check your SBOM immediately. It is much faster than manual checking.
To be honest, the industry stayed away from this for a long time. It felt like extra paperwork. However, major cyberattacks like SolarWinds changed the game. Now, the U.S. government and global agencies like CERT-In require these lists for many projects.
A good Software Bill of Materials isn't just a random text file. It must follow certain rules to be useful. According to NTIA (National Telecommunications and Information Administration) standards, there are three main parts: data fields, automation support, and practices.
1. Mandatory Data Fields
Every entry in your list needs specific details. You need the supplier name, the component name, and the version string. You also need unique identifiers. Why? Because two different companies might name their library "LoginTool." Without a unique ID, your security scanner will get confused.
2. Automation Support
You must provide the list in a format that computers understand. We usually use formats like CycloneDX or SPDX. These are the "languages" of the Software Bill of Materials. If you try to manage this in a Word document, you'll fail. Trust me, we've tried, and it’s a nightmare.
3. Practices and Processes
How often do you update the list? You should create a new one every time you build a new version of your software. If you change one tiny library, the old list is useless.
Also Read: Security Automation: How to Protect Your Data Without the Burnout
We have all been there: a news alert pops up about a massive data breach. Usually, it's not the main app that broke. It was a tiny piece of code deep inside the system. This is a supply chain attack.
A Software Bill of Materials acts as a map for your supply chain. It helps you see where your code comes from. Most modern apps are 70% to 90% open-source code. That is a lot of code you didn't write. Using an SBOM helps you manage the "licenses" of that code too. You don't want to accidentally use code that forces you to give away your intellectual property, right?
How does a Software Bill of Materials actually make your life easier? Let's look at a few ways.
In my view, the biggest benefit is transparency. It builds trust between the software seller and the buyer. When you show a client your Software Bill of Materials, you're saying, "We have nothing to hide. We know exactly what we're selling you."
When you start your Software Bill of Materials journey, you'll hear these two names a lot. Which one should you pick?
| Feature | SPDX | CycloneDX |
|---|---|---|
| Origin | Linux Foundation | OWASP Foundation |
| Focus | Licensing and IP | Security and Vulnerabilities |
| Complexity | Very detailed | Lightweight and fast |
SPDX is great if your legal team is worried about copyrights. CycloneDX is often better for security teams who want to find bugs quickly. Most modern tools support both, so don't sweat the choice too much early on.
Also Read: What is File Integrity Monitoring (FIM)? Security Guide
Here is a secret: just because a library has a bug doesn't mean your app is at risk. Sometimes, you use a library but don't use the "broken" part of it. This is where Vulnerability Exploitability eXchange (VEX) comes in.
A VEX is a companion to your Software Bill of Materials. It tells the reader, "Yes, we use this library, but we aren't affected by that specific bug." This stops your security team from chasing ghosts. It saves hundreds of hours of useless work.
I won't lie to you; it isn't always easy. One big challenge is "transitive dependencies." This refers to the library that your library uses. It's like a family tree that never ends. Getting a full Software Bill of Materials that goes all the way down is hard.
Another issue is keeping things private. Some companies worry that an SBOM gives hackers a "road map" to attack them. While that's a fair concern, the reality is that hackers usually find these things anyway. It's better for you to have the map first.
We are seeing new types of lists pop up. There's HBOM for hardware and AIBOM for Artificial Intelligence models. As we move forward, every part of our tech stack will have an "ingredient list."
The Software Bill of Materials is moving from a "nice to have" to a "must-have." We are roughly at the stage where every serious developer needs to automate this. If you are still doing it manually, you are behind the curve.
At the end of the day, a Software Bill of Materials is about taking control. We can't stop hackers from trying to find holes in open-source code. However, we can make sure we aren't flying blind. By keeping a clear list of what is in our software, we protect our clients and our reputation.
Our company believes in a "security-first" culture. We don't just build tools; we build trust. We focus on providing the clarity you need to stay safe in a complex world. When you partner with us, you get total transparency and a team that cares about your data as much as you do.
Want to secure your software supply chain?
Contact our team today for a full security audit!
The main goal is transparency. It allows organizations to see what's inside their software so they can manage security, legal, and operational risks.
No. It only lists the names, versions, and details of the components. It does not reveal your "secret sauce" or private code logic.
You should generate a new one with every build or release. If the code changes, the Software Bill of Materials must change too.
For many government contractors and regulated industries, yes. For others, it is rapidly becoming an industry standard for best practices.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts