.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Red Team exercises are the ultimate way to see if your company can actually stand up to a real-life cyber attack. Imagine you have built a high-tech fortress. You have cameras, locks, and guards. But how do you know if they work? You hire someone to try and break in. That is exactly what we mean when we talk about this type of security testing.
In the world of IT, things move fast. Hackers are always finding new ways to get past firewalls. You might think your data is safe because you haven't had a breach yet. But is that enough? To be honest, most companies only realize they have a hole in their fence after the intruder is already inside the house.
Here is the thing: a Red Team doesn't just look for bugs in your code. They look for ways to trick your people, bypass your badges, and slip through your network undetected. It is a full-scale simulation of a "bad guy" mindset. Have you ever wondered what a professional hacker sees when they look at your website?
We have all been there—thinking a strong password is enough. In reality, modern threats are much more complex. A Red Team acts as an ethical group of hackers. Their goal is to challenge your "Blue Team" (your defenders). By doing this, they show you exactly where your armor is thin.
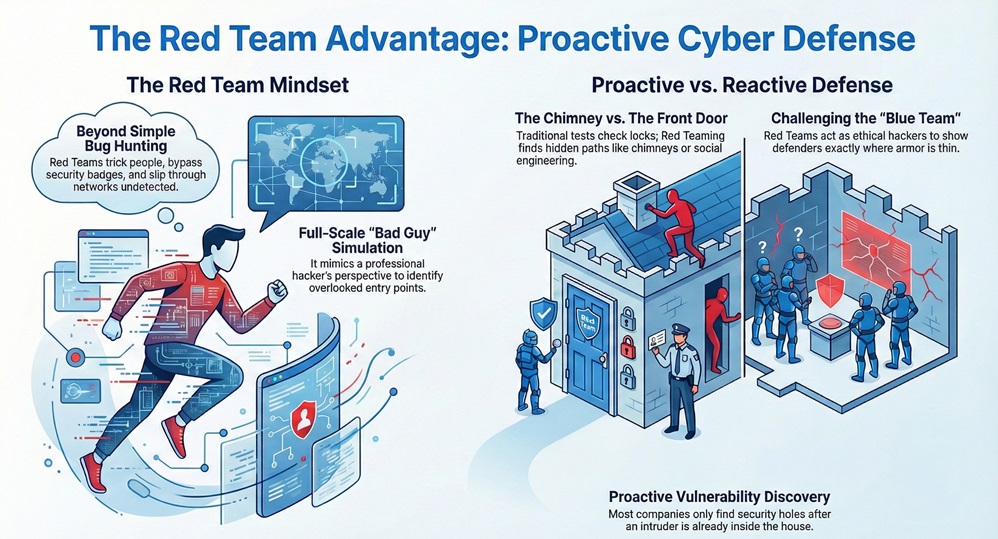
Roughly speaking, traditional security tests are like checking if the front door is locked. A red team exercise is more like seeing if someone can climb through the chimney or trick the gardener into handing over the keys. It provides a level of reality that a simple scan just can't match.
Do you want to wait for a real attack to find your flaws? Most leaders would say no. That is why these exercises have become a gold standard for companies that handle sensitive data. It’s about being proactive rather than reactive.
Also Read: How the Cato Client Becomes the Identity Anchor for Zero Trust Access
The process is not just random hacking. It is a structured journey. Let's look at how these experts move from a blank screen to deep inside a network. Usually, they follow a path that mimics the "Cyber Kill Chain."
1. Information Gathering (Reconnaissance)
First, the team gathers as much public data as possible. They look at social media, employee lists, and public IP addresses. This is where they find the "low-hanging fruit." For example, they might find an employee who posted a picture of their office badge on LinkedIn.
2. Planning the Attack
Now, they decide on the best path. Will they send a fake email? Will they try to plug a "lost" USB drive into a computer in the lobby? This phase is all about strategy. They want to find the path of least resistance.
3. Gaining Access
This is where the action starts. The Red Team might use a "phishing" email to steal credentials. Or, they might find a tiny flaw in a web application. Once they get one foot in the door, they don't stop. They want to see how far they can go.
4. Staying Inside (Persistence)
A real hacker doesn't just steal a file and leave. They want to stay hidden for months. The team sets up "backdoors" so they can come and go as they please. This tests if your security software can spot unusual behavior over a long period.
5. Completing the Mission
In the final stage, the team reaches the "crown jewels." This might be your customer database or your financial records. They don't actually steal it, of course. They just prove that they could have.
Also Read: Device-Aware WAN Firewall Policies in Cato SASE
Many people get these two confused. It is easy to see why! Both involve hacking into systems. However, the scope is very different. Think of a Penetration Test (Pen Test) as a safety inspection. The inspector walks around, checks the fire extinguisher, and ensures the lights work.
On the other hand, a Red Team exercise is a surprise fire drill at 3:00 AM. It’s unannounced and tests the people, not just the equipment. While a Pen Test finds as many vulnerabilities as possible, the red group focuses on one specific goal: getting to the data.
| Feature | Penetration Testing | Red Team Exercise |
|---|---|---|
| Goal | Find all technical bugs | Test detection and response |
| Duration | 1-2 weeks | Several weeks to months |
| Scope | Specific apps or networks | People, physical, and digital |
| Awareness | IT team usually knows | Very few people know |
Which one does your company need? Usually, you start with Pen Tests to fix the easy stuff. Once you're confident, you bring in the red squad to test your actual readiness.
These experts use a mix of software and human psychology. Some tools are used to scan for open ports. Others are used to crack passwords. Interestingly, some of the most effective tools are not digital at all.
Social engineering is a huge part of the Red Team toolkit. This involves "hacking the human." It’s often much easier to call an employee and pretend to be from the IT help desk than it is to crack a 20-character password. Have you ever considered how easily your team might give away info over the phone?
They also use physical tools. This includes lock picks, RFID cloners for badges, and tiny devices that hide behind a computer to record every keystroke. It’s like a spy movie, but the goal is to make your business safer.
Why put your staff through this stress? The benefits are huge. First, it improves your "Mean Time to Detect" (MTTD). This is just a fancy way of saying how fast you catch a thief. If it takes your team three weeks to notice a hacker, that is three weeks of damage.
Second, it trains your defenders. Your Blue Team gets real-world practice. They learn what a real attack looks like in their logs. This builds "muscle memory." When a real threat arrives, they won't panic; they'll follow the plan.
Lastly, it helps you spend your budget wisely. You might find out that your expensive new firewall didn't stop the attack, but a simple $10 training course for employees would have. This helps you put money where it actually matters.
At our core, we believe that security is not a product you buy; it is a habit you practice. Understanding what a Red Team does is the first step toward a safer future. We have seen how these simulations turn vulnerable businesses into hard targets. It’s about more than just technology. It’s about building a culture where everyone is a part of the defense.
To be honest, the "bad guys" are already practicing. Shouldn't you be practicing too? We are committed to helping our clients stay one step ahead of threats. Our focus is always on your safety and your peace of mind. Let’s work together to make sure your "fortress" is as strong as you think it is.

No. These are professionals. They follow strict rules of engagement. They prove they can access data without actually damaging or leaking it.
Most experts suggest once a year. However, if you make big changes to your network, you might want to do it sooner.
Yes. You need someone to "play defense" for the exercise to be useful. If you have no defenders, you already know you'll lose!
It is often more common for larger firms. That said, smaller companies can use "Purple Teaming," where the attackers and defenders work together to learn.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts