.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
When organizations scale device fleets across multiple departments, locations, and administrators, centralized access becomes a liability. A single super-admin model introduces unnecessary risk: what if someone misconfigures a profile, or a junior admin gains access to devices or data beyond their responsibility?
Role-Based Access Control (RBAC) solves this by delegating administrative tasks based on job role, department, or location. Miradore provides a secure and structured way to assign management privileges — giving your IT staff just the access they need, and nothing more.
In this blog, we’ll break down how Miradore enables granular permission control, minimizes insider risk, and supports multi-tenant teams in regulated or high-growth environments.
Device management platforms often require multiple IT personnel working across offices, countries, or business units. Without role controls, every admin sees and can manage every device — even if it’s irrelevant to their scope.
The risk?
RBAC eliminates these risks by defining who can do what — and where.
Don’t let admin mistakes compromise your fleet security. Fill out the form to explore Miradore’s RBAC features today.
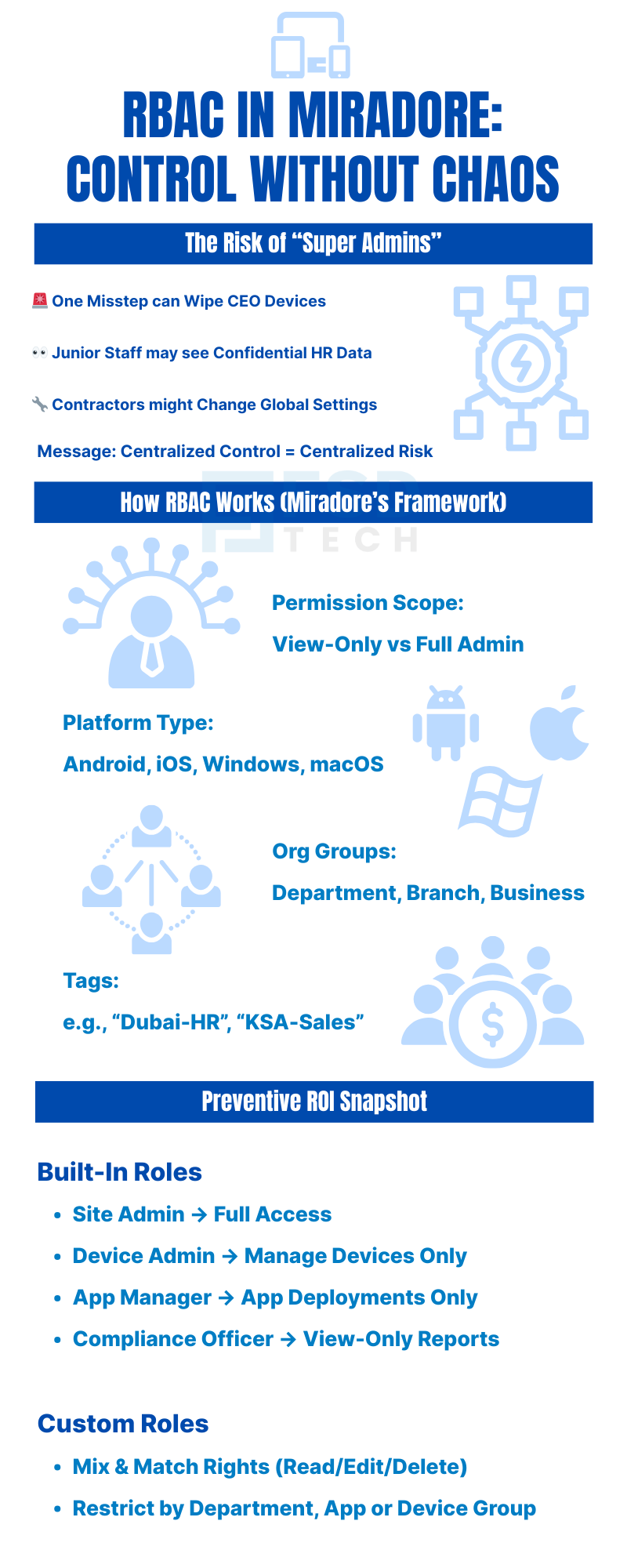
Miradore allows you to create and assign roles based on:
Admins can assign these roles from the Miradore console, with changes taking effect immediately.
Example: A school IT lead can manage tablets used by students, but cannot access teacher laptops or corporate-owned iPhones.
Miradore provides predefined roles for common use cases:
| Built-In Role | Permissions Summary |
|---|---|
| Site Admin | Full access to all devices and policies |
| Device Admin | Manage devices but not system-wide settings |
| Application Manager | App deployment and app restrictions only |
| Compliance Officer | View-only access to compliance dashboards and reports |
Need something more tailored?
Create custom roles that mix and match:
Miradore lets you segment devices into logical units using:
Roles can then be tied to these units so that a regional admin sees only what’s relevant to their scope.
Scenario: A compliance lead in Saudi Arabia has access only to SAMA-related reporting dashboards and cannot view or alter UAE endpoints.
To meet internal and external compliance requirements, Miradore logs every admin action — from device wipes to policy changes.
You can:
These logs are essential for incident response and regulatory documentation (e.g., ISO 27001, GDPR, or GCC-specific policies).
A managed service provider (MSP) supports clients across five GCC countries. They structured Miradore as follows:
This RBAC model reduced data exposure risks and ensured every stakeholder only saw the information relevant to their function.
Next Steps
Centralizing management is useful—but centralizing risk is dangerous. With Miradore’s RBAC features, you get the best of both worlds: a unified console with finely tuned access per user, region, or responsibility.
Empower your IT team without losing control.
Want to see RBAC in action for your organization? Book a Free session with our Miradore experts. Schedule your consultation today.
Yes. Miradore lets you define access by platform, so an admin can be restricted to managing only Android devices while another oversees Windows endpoints. This is useful when responsibilities are divided between mobile and desktop teams.
Yes. Miradore’s multi-tenant architecture allows managed service providers to set up isolated environments for each client. Within each site, roles can be created and assigned separately—ensuring complete segregation of access.
Absolutely. Miradore maintains a detailed activity log that records every admin action—including who made the change, what was changed, when it occurred, and the affected device(s). This is vital for compliance audits and post-incident investigations.
Built-in roles provide predefined permission sets for common administrative needs. Custom roles offer flexibility to define specific capabilities, allowing organizations to match access precisely to job responsibilities. You can even restrict certain UI elements or hide modules.
Yes. Miradore supports role stacking, which allows a user to inherit privileges from multiple assigned roles. This is useful when someone needs overlapping access—for example, a compliance officer who also manages applications in a certain department.
Yes. RBAC supports least-privilege principles required by standards like ISO 27001, NESA, and SAMA. By controlling access to sensitive data and maintaining audit trails, it helps satisfy both internal and external regulatory requirements.
Changes in roles and permissions are applied immediately. As soon as an update is saved, the affected user’s session reflects the new permissions. This helps in swiftly onboarding new staff or revoking access for offboarding scenarios.
Yes. You can create read-only roles with access restricted only to specific areas of the dashboard, such as compliance reports. This allows auditors or non-technical personnel to review data without exposing broader device management functions.

Anas is an Expert in Network and Security Infrastructure, With over seven years of industry experience, holding certifications Including CCIE- Enterprise, PCNSE, Cato SASE Expert, and Atera Certified Master. Anas provides his valuable insights and expertise to readers.
Share it with friends!
.webp&w=3840&q=75)
🕓 March 25, 2026

🕓 March 22, 2026

🕓 March 20, 2026
share your thoughts