.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
Imagine It’s 2:00 AM on a Tuesday. In a high-tech manufacturing plant in Riyadh, a robotic arm begins to move erratically, deviating from its programmed path by mere millimeters. Simultaneously, halfway across the world in a corporate office in London, an IT security dashboard lights up.
In the old days, these two worlds—Information Technology (IT) and Operational Technology (OT)—didn't speak the same language. The IT manager cared about data privacy and email servers; the plant manager cared about uptime and physical safety. They lived in different buildings, used different cables, and followed different rules.
But today, Industry 4.0 has smashed those silos. Your factory floor is now part of your digital network. While this "IT/OT convergence" brings incredible efficiency, it also creates a massive security gap. How do you protect a 20-year-old industrial controller that was never designed to see the internet?
The answer lies in SASE (Secure Access Service Edge). By converging networking and security into a single cloud-native platform, SASE provides the "glue" that allows IT and OT to work together without risking a catastrophic breach.
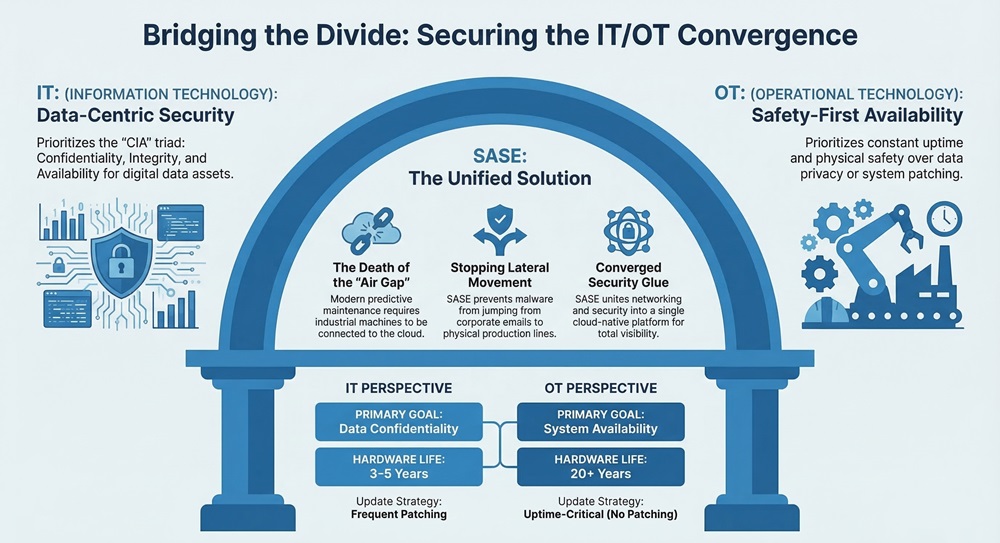
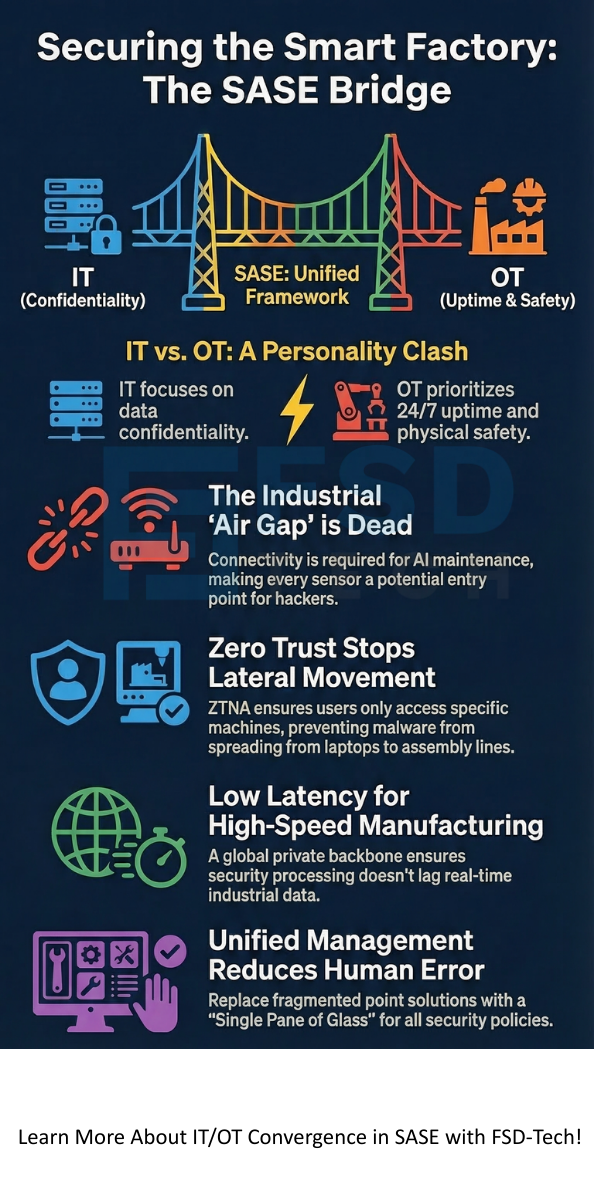
To understand why we need SASE, we first have to admit that IT and OT have a "personality clash."
The IT Perspective (Data First)
IT is all about the "CIA" triad: Confidentiality, Integrity, and Availability. If a laptop gets infected, the IT team's first instinct is to isolate it, even if that person can't work for an hour. Updates are frequent, and hardware is replaced every three to five years.
The OT Perspective (Safety First)
In the world of OT, the priority is "Availability" above all else. If a production line stops, it costs thousands of dollars per minute. You can’t just "patch" a programmable logic controller (PLC) on a Wednesday afternoon because it might crash the system. These machines are often built to last 20 years, meaning many are running "legacy" software that is a playground for modern hackers.
The "Air Gap" Myth and the Industry 4.0 Reality
For decades, industrial security relied on the "air gap"—the idea that if the factory machines weren't connected to the internet, they couldn't be hacked.
Here’s the thing: the air gap is dead. To get the benefits of AI-driven predictive maintenance and real-time supply chain tracking, your OT systems must talk to the cloud. This connectivity is a double-edged sword. Every sensor you add to a machine is a potential "entry point" for an attacker.
We've all seen the headlines. A small malware infection in a corporate email system (IT) moves laterally through the network until it hits the production line (OT), causing a total shutdown. This is why a unified approach isn't just a "nice to have"—it's a survival requirement.
Talk to Our Cato SASE Specialist
Many companies try to secure this convergence using "point solutions." They buy a VPN for remote technicians and a stack of firewalls for the factory floor.
In my experience, this "sweat and tears" integration approach leads to three major problems:
Also Read: Auto-Adaptive Threat Prevention: How SASE Stops Modern Cyberattacks
SASE (Secure Access Service Edge) solves these problems by moving security to the cloud and the edge. Instead of a "castle and moat," SASE creates a secure "fabric" that wraps around every user, every machine, and every cloud application.
1. Zero Trust Network Access (ZTNA)
This is the heart of IT/OT convergence. In a SASE model, no one is trusted by default. If a third-party contractor needs to update the software on a specific robot, ZTNA ensures they only see that robot. They can't wander around the rest of the network. This "micro-segmentation" stops malware from spreading from a laptop to the assembly line.
2. Global Private Backbone
SASE providers like Cato Networks use a global private backbone. This means your OT data doesn't just wander across the public, "dirty" internet. It travels on a fast, optimized path, ensuring the low latency required for high-speed manufacturing.
3. Unified Management (The Single Pane of Glass)
With SASE, your IT and OT security policies are managed from one dashboard. You don't need a different team for the factory and the office. One policy follows the user or the device, regardless of where they are.
Also Read: Vendor Consolidation: Why SASE is the Future of IT
Consider a global paint manufacturer like the Flügger Group. They had a legacy MPLS network that was rigid and expensive. Every time they integrated a new partner or opened a location, it took months of "sweat and tears" to get the networking and security right.
By switching to a SASE architecture, they consolidated their WAN and internet traffic into the cloud. They deployed "sockets" at their locations that instantly connected to the global backbone. The result? They gained total visibility into their production sites, reduced their costs, and could finally secure their remote technicians without the headache of traditional VPNs.
When we talk about the Total Cost of Ownership (TCO), we have to look beyond the subscription price.
The "Smart Factory" is no longer a dream; it is the standard. But as we embrace the power of Industry 4.0, we must respect the risks that come with it. IT/OT convergence isn't just a technical challenge—it's a business challenge.
By adopting a SASE architecture, you are choosing a path of "imperfect perfection"—a system that is agile enough to grow with you but rigid enough to stop a hacker in their tracks. We've all been there, struggling with legacy systems and mounting costs. But it doesn't have to be that way.
At Cato, we believe in building a perimeter that follows you, protects your most vulnerable assets, and lets your team focus on innovation rather than troubleshooting. Thus, we can say that SASE is the ultimate bridge between the digital office and the physical floor.
To be honest, it’s actually simpler than the alternative. Managing five different security tools is complex. Managing one SASE platform is a relief for overstretched IT teams.
Yes. SASE protects legacy OT by "cloaking" them at the network level. The machines don't need to change; the SASE "socket" handles the security and encryption for them.
Instead of a clunky VPN that gives a contractor full network access, SASE uses ZTNA. You grant "least privilege" access to a specific machine for a specific time. It’s safer and much easier to audit.
With SASE, the "firewall" is in the cloud (FWaaS). You still have a physical "socket" at the site to connect to the network, but the heavy security processing happens in the SASE cloud, which is always updated against the latest threats.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts