.webp&w=3840&q=75)
How ClickUp Enables Outcome-Based Project Management (Not Just Task Tracking)
🕓 February 15, 2026
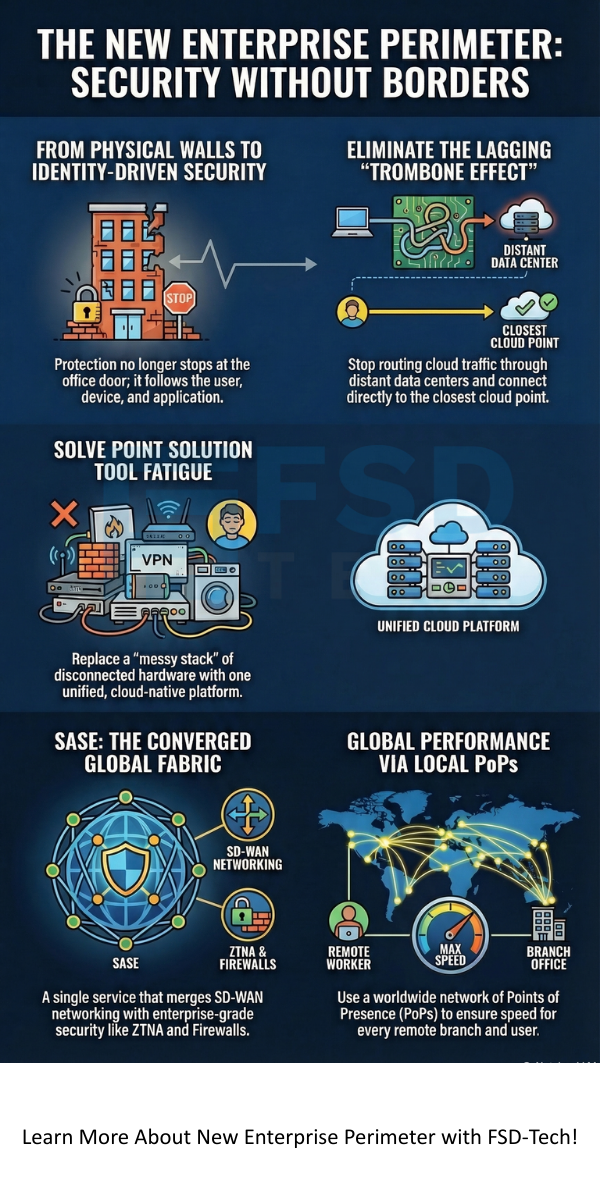
The New Enterprise Perimeter isn't a physical wall around your office anymore; it's a flexible, identity-driven boundary that follows your users and data wherever they go. For decades, IT teams built "moats" around data centers. They used firewalls and stacks of hardware to keep the bad guys out. But then, something changed. Apps moved to the cloud. Employees started working from home or coffee shops.
Suddenly, the old perimeter didn't work. To be honest, it was like trying to protect a house when half the family lives in other cities. This is why we need a fresh approach. Have you ever felt like your network is actually slowing your business down? You're not alone. Many teams are struggling with "point solution fatigue," where they have too many tools that don't talk to each other.
In this guide, we'll look at how the Secure Access Service Edge, or SASE, fixes this. We'll explore why the old ways are failing and how a unified, cloud-native approach can make your life easier. It's time to stop fighting with your network and start letting it work for you.
In the past, the perimeter was a clear physical line. It was easy to manage because everything—servers, files, and people—sat in one building. But today, "the office" is everywhere. Your data lives in AWS, Azure, or Office 365. Your employees use laptops in the field and tablets at home.

The New Enterprise Perimeter is now a "multi-perimeter" reality. It includes:
This shift means we can't rely on hardware boxes at every location. It’s too expensive and too slow to manage. Instead, we need a solution that lives where your data lives: in the cloud.
Many companies are still "weighed down" by point solutions. Imagine buying a separate tool for every single security need. You'd have one for firewalls, one for web filtering, and another for remote access. Pretty soon, you're managing ten different dashboards.
The Complexity Trap
When you pile up these tools, you create a "complexity burden". You have to evaluate vendors, buy the gear, install it, and then fix it when it breaks. It’s a lot of work. In my view, this complexity is a hidden cost that robs your team of time. Instead of building new features, they're just keeping the lights on.
The "Trombone Effect"
Old networks often forced all traffic through a central data center for security. If a user in London wanted to access a cloud app, their traffic would travel to a data center in New York just to be inspected. This is called the "trombone effect." It adds lag, frustrates users, and wastes money.
Also Read: Cloud-Native Architecture: Why SASE is the Future of Global Networking?
Gartner defined SASE in 2019 to solve these exact problems. SASE converges networking and security into one global cloud service. It’s like a Swiss Army knife for your network.
Here is what makes it different:
The manufacturing industry is a great example of why this matters. With "Industry 4.0," factories are becoming smart. They use AI, IoT sensors, and robots to stay competitive.
But here's the catch: most of these smart devices weren't built with security in mind. They are easy targets for hackers. Also, many factories are in remote areas where getting a fast connection is a nightmare.
SASE helps manufacturers by:
Picture this: a factory in Vietnam needs to send huge CAD files to a design team in Germany. With SASE, that data travels over a secure, optimized private network, not the "wild west" of the public internet.
Also Read: Maximum Transmission Unit: MTU Settings for Faster Networks
Cato Networks provides the first true SASE platform. They don't just "bolt on" security to a network; they built it as one unified service from the start.
We've all seen vendors claim they have "converged" solutions, but they're often just different products stuck together with tape. Cato is different. Their cloud-native platform includes:
By choosing a single-vendor SASE, you eliminate the "sweat and tears" of integration. You get one policy, one management console, and one global network.
At Cato Networks, we're focused on making your digital transformation simple. We believe that networking shouldn't be a burden. It should be an asset that helps your company grow faster. Our platform is built for the "what's next" of business, ensuring you're always ready for new challenges. Let’s stop managing boxes and start managing your business.
Talk to a Cato SASE Specialist
It refers to the fact that corporate data and users are now spread across various locations, clouds, and devices, rather than being confined to a single physical office.
It uses Zero-Trust Network Access (ZTNA) to ensure that users are verified and only have access to the specific apps they need, regardless of their location.
Yes. Many companies migrate from expensive MPLS to SASE because it offers better cloud connectivity and lower costs while maintaining high performance.

Surbhi Suhane is an experienced digital marketing and content specialist with deep expertise in Getting Things Done (GTD) methodology and process automation. Adept at optimizing workflows and leveraging automation tools to enhance productivity and deliver impactful results in content creation and SEO optimization.
Share it with friends!
share your thoughts